Defender for Office 365 fundamentals
The use case
In cybersecurity we consider the Internet and office applications as the biggest attack surface as most of us have interactions to these two matters, making them extremely comprehensive and diverse and unfortunately lucrative for attackers to try to breach in our actions. We try to counter them with a variety of security measures and perimeters that must be increasingly sophisticated and technologically advanced to keep us safe.
Capabilities
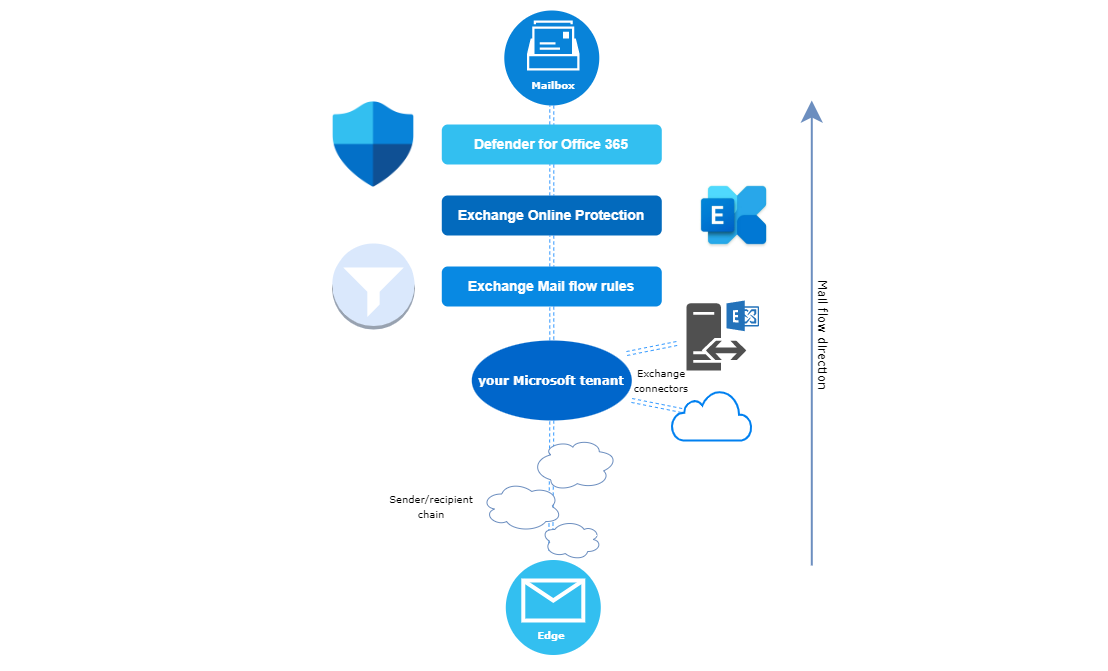
The capabilities consitute of the use case, just translated into an applicable product or feature, hosted in the cloud. Evidently, Microsoft wants to protect the whole Office 365 suite, especially Exchange (EOP, exchange online protection) but also the collaboration fields. If you are already familiar with a mail protection solution, you will quickly get to grips with the core capabilities. Defender for Office 365 is essentially here to:
- Leverage email and collaboration security
- Enables admins to get more visibility across Office 365
- Automate investigations and responses on suspicious events
- Launch inside attack simulations and rise user awareness
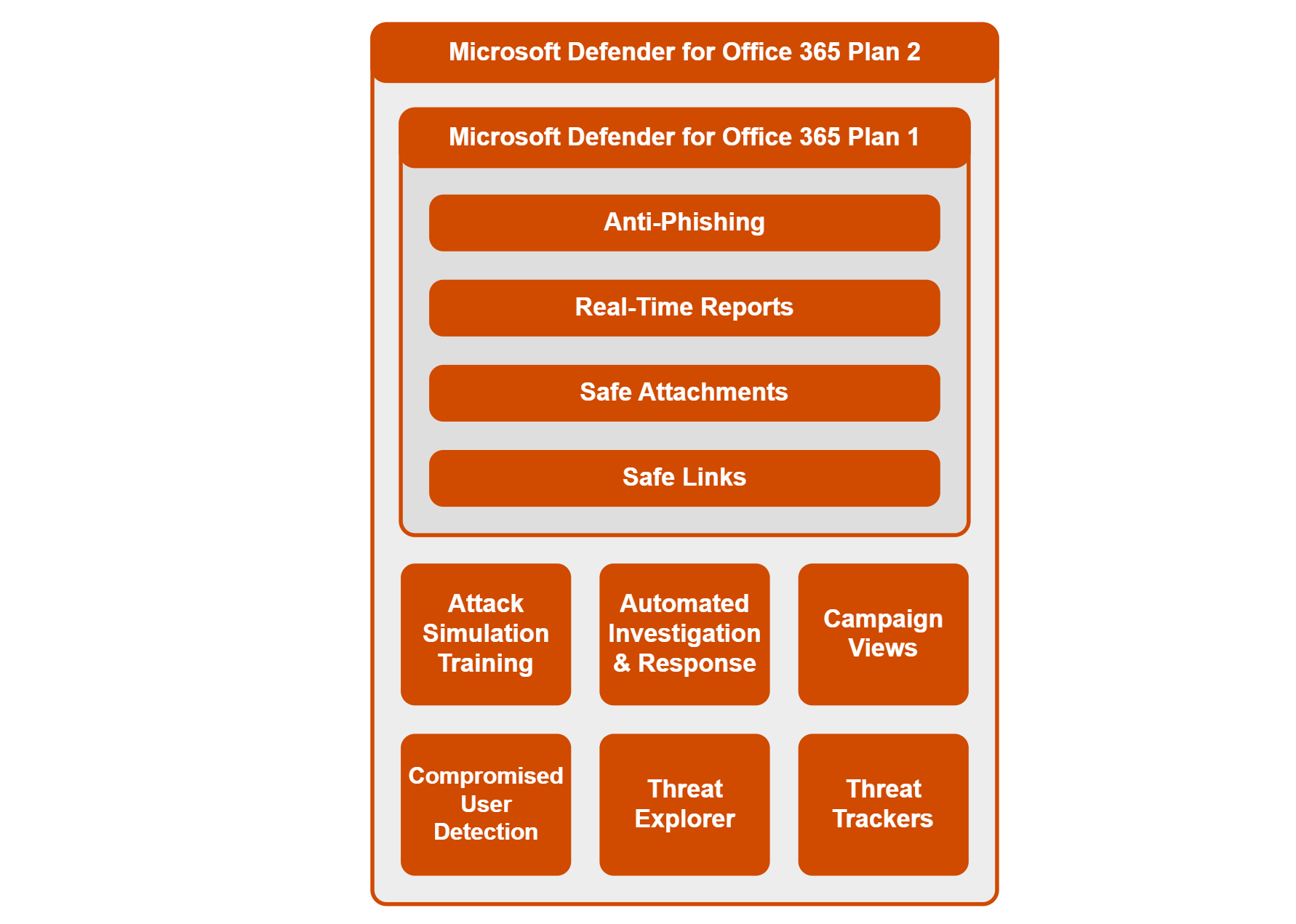
At the time of this post (March 2022) Microsoft Defender for Office 365 includes this set of features:
Pre reqs
Planing to move to Defender for Office 365 could imagine two starting positions: 1. your organization does not have a mail protection solution at the time or is still building up their Microsoft tenant or 2. there is an alternate product your organization has in place and the plan is to migrate to Defender for Office 365. Then you might prepare an assessment of what policies and configurations are currently working and you may try to rethink whats the strategy and how your future with Microsoft could look like.
For both cases you need a Defender for Office 365 license plan.
Talking technology
Moreover you should understand the technologies, that protect mailing and collaboration. Namely, I mean general terms like spam/bulk/junk mails, spoofing or phishing or mail attached with malware, detected through BCL or SCL for inbound and outbound messages and actions to take like quarantine or rejecting up to functions like ZAP or dynamic delivery. Authentication methods, in particular: SPF, DKIM, DMARC or DNSBL, RBLs that help to identify suspicious or malicious senders and allow/block lists that are used. Additionally, systems that are related with connectors, rules and policies, furthermore content analysis and encryption. All those terms are in some way used in most mail protection applications.
Microsoft 365 Defender portal
The whole Microsoft 365 security stack, where Defender for Office 365 is part of, is represented in the Microsoft 365 Defender portal.
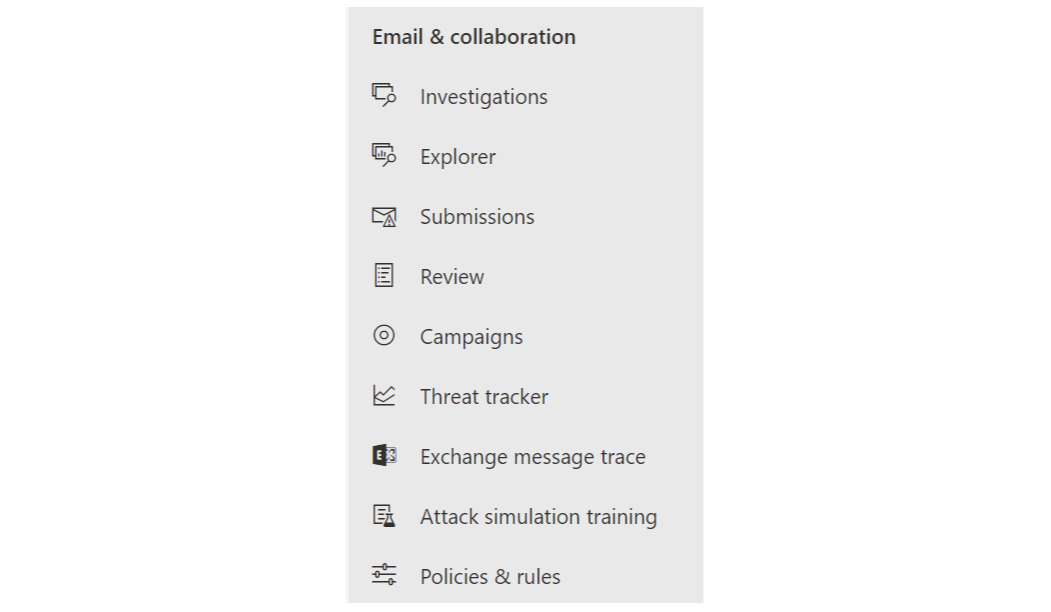
If we move from the security perspective to the engineering side, there is also the Exchange admin center.
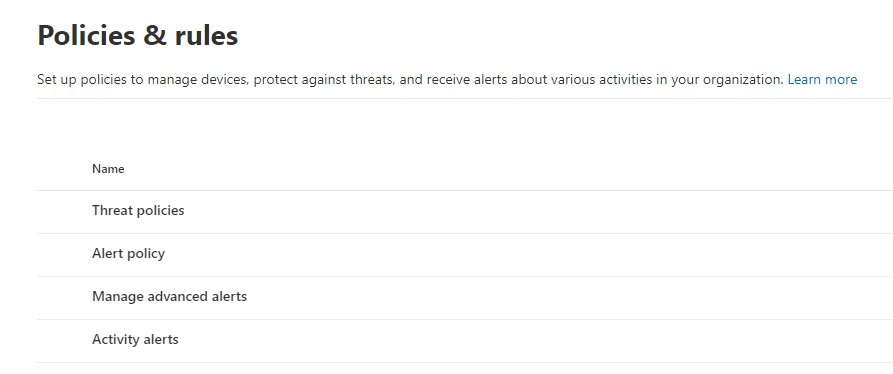
Policies & rules - Threat policies
You will find all the configs under Policies & rules.
- Threat policies - all about Defender for Office 365 settings
- Alert policies - built-in alert policies
- Manage advanced alerts - a reference to Office 365 controls within Defender for Cloud Apps
- Activity alerts - Custom alert policies based on conditions
Templated policies
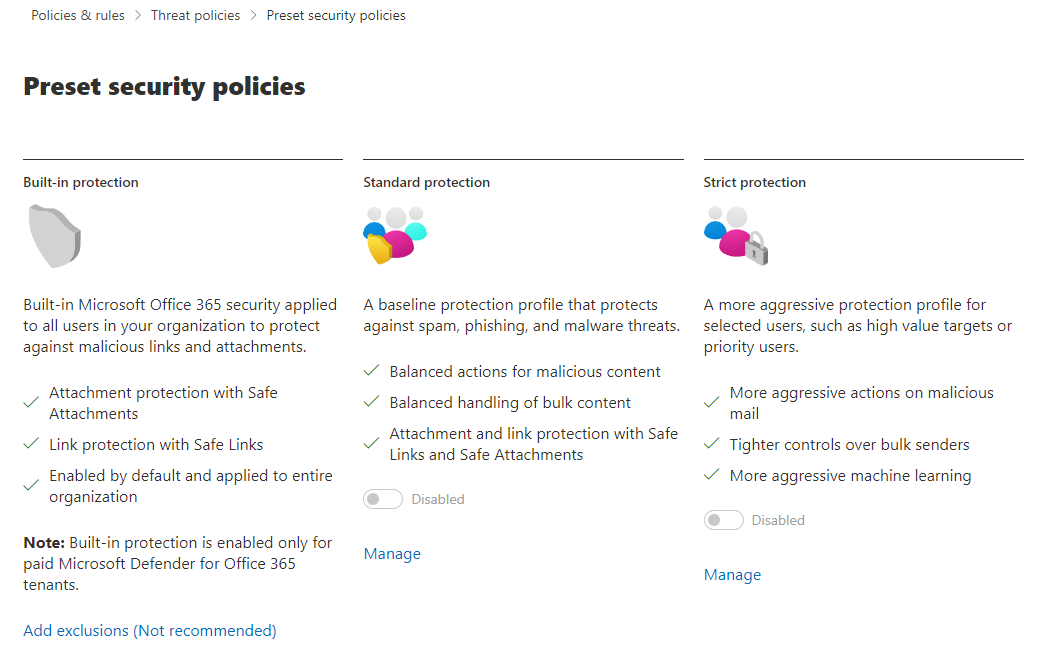
Preset Security Policies
Microsoft offers preset security policies in 3 categories: Built-in protection (always on, but allows for exclusions), standard protection (more balanced) and strict policies (rigorous and aggressive behavior). Want to go easy? Just apply those policy templates to users, groups or domains. Microsoft also differentiates between EOP and Defender for Office 365 applications.
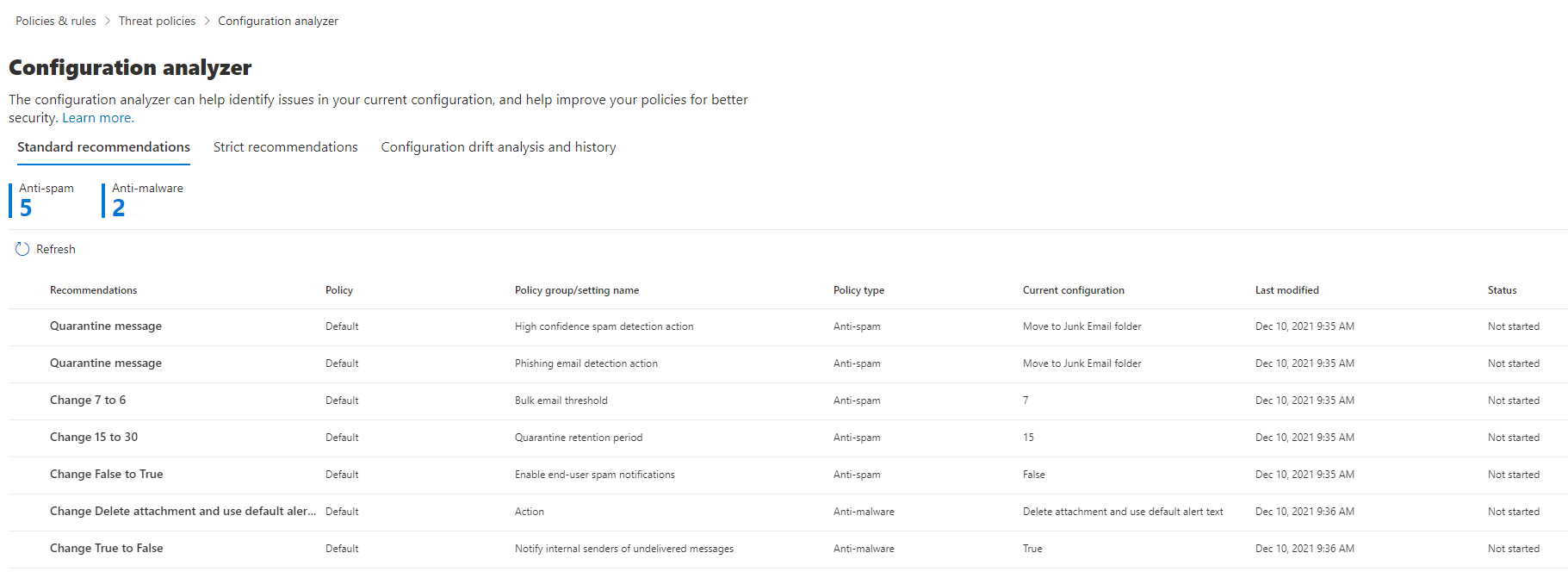
Configuration analyzer
The configuration analyzer could be compared to the Microsoft Secure Score. You see configuration recommendations (also in categories of standard and strict), that should be taken to optimize your posture. Under configuration drift analysis and history, we have a history of audit changes.
Policies
The core measurements are found in the following policies. It's the most important part to set up. Those are always assignable to users, groups, and domains and allow for exclusions.
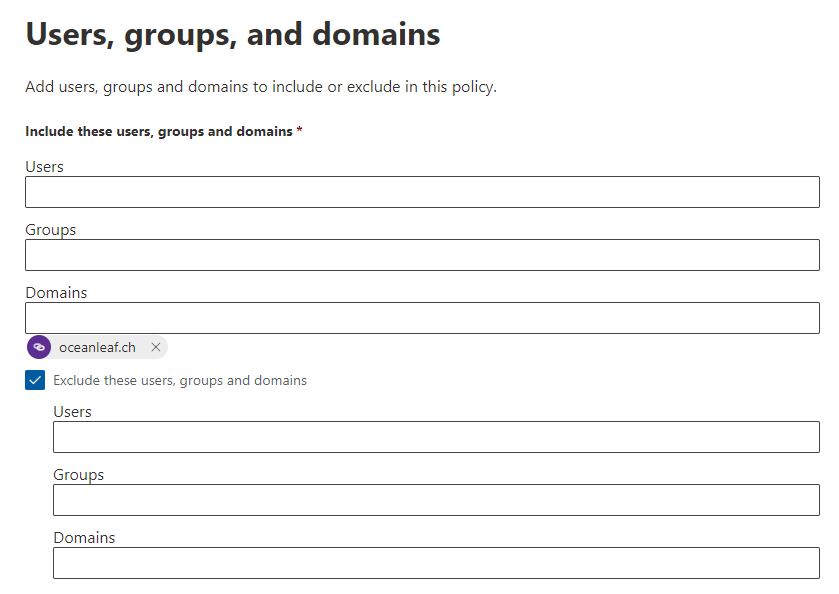
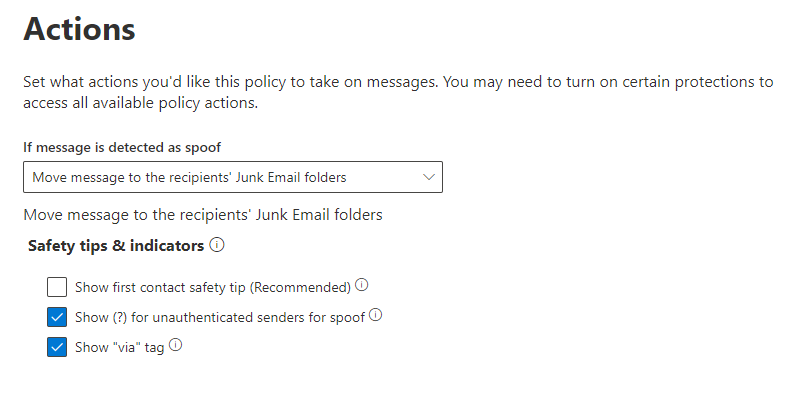
Anti-phishing
Anti-phishing policy uses the spoof intelligence, to recognize mails that are originated from an external source but pretend to be an internal sender.
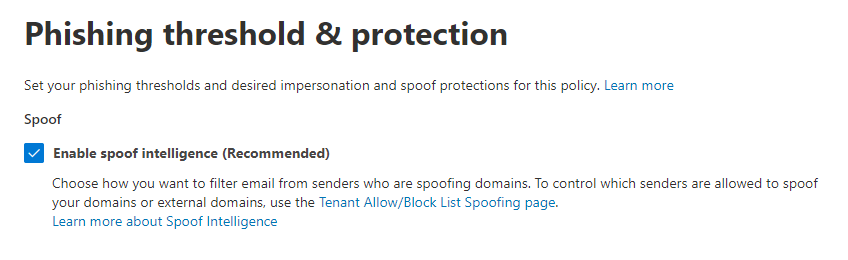
Subsequently select an action to take on spoofed mails. To rise the awareness, certain safety tips & indicators are available to enable.
Anti-spam
Anti-spam policies are possible for both directions; inbound and outbound.
Inbound policy
In the inbound policy we manage the bulk email threshold, which is based on BCL, bulk complaint level. Every inbound message receives a bulk complaint level (the higher the rating, the more likely it is bulk). The spam score is evaluated on several properties, including the ones in the image, which you can specify:
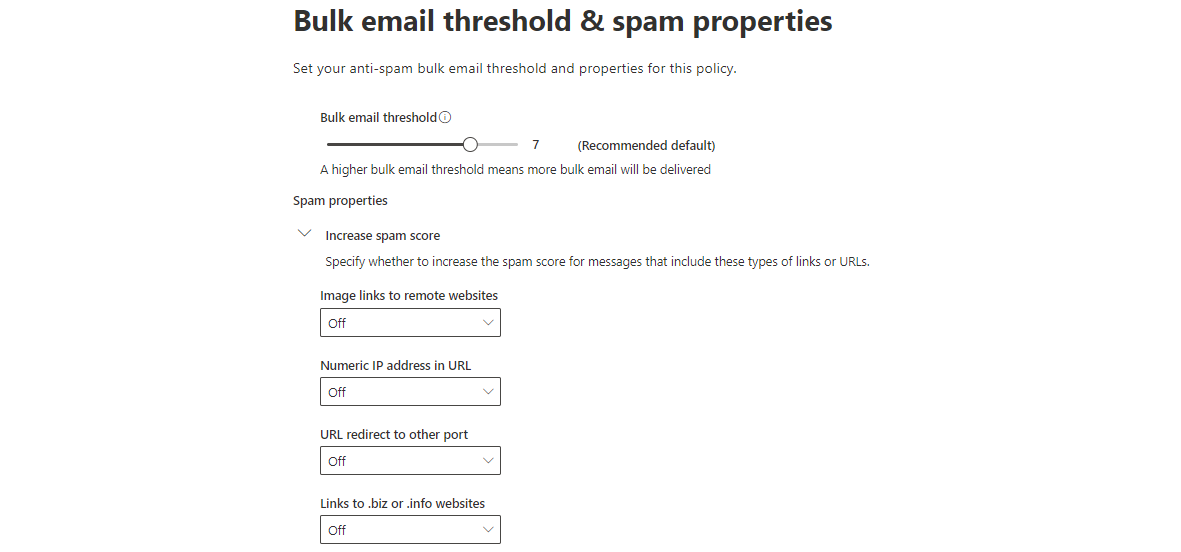
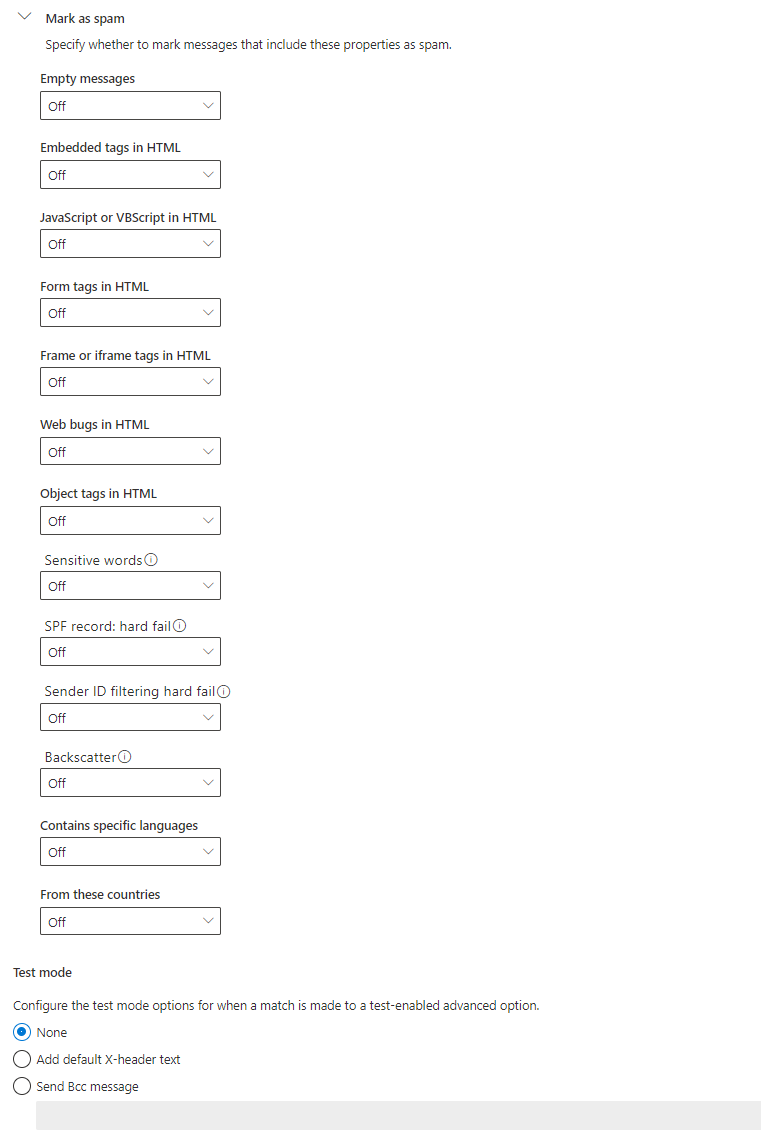
Furthermore, we specify which type of messages, or message attributes should be marked as spam. This is fully open to you. Just at the bottom, there is a test mode, as all of the settings can be set to "On", "Off" or "Test". To draw a conclusion of the "Test" cases, you can prepare the action here.
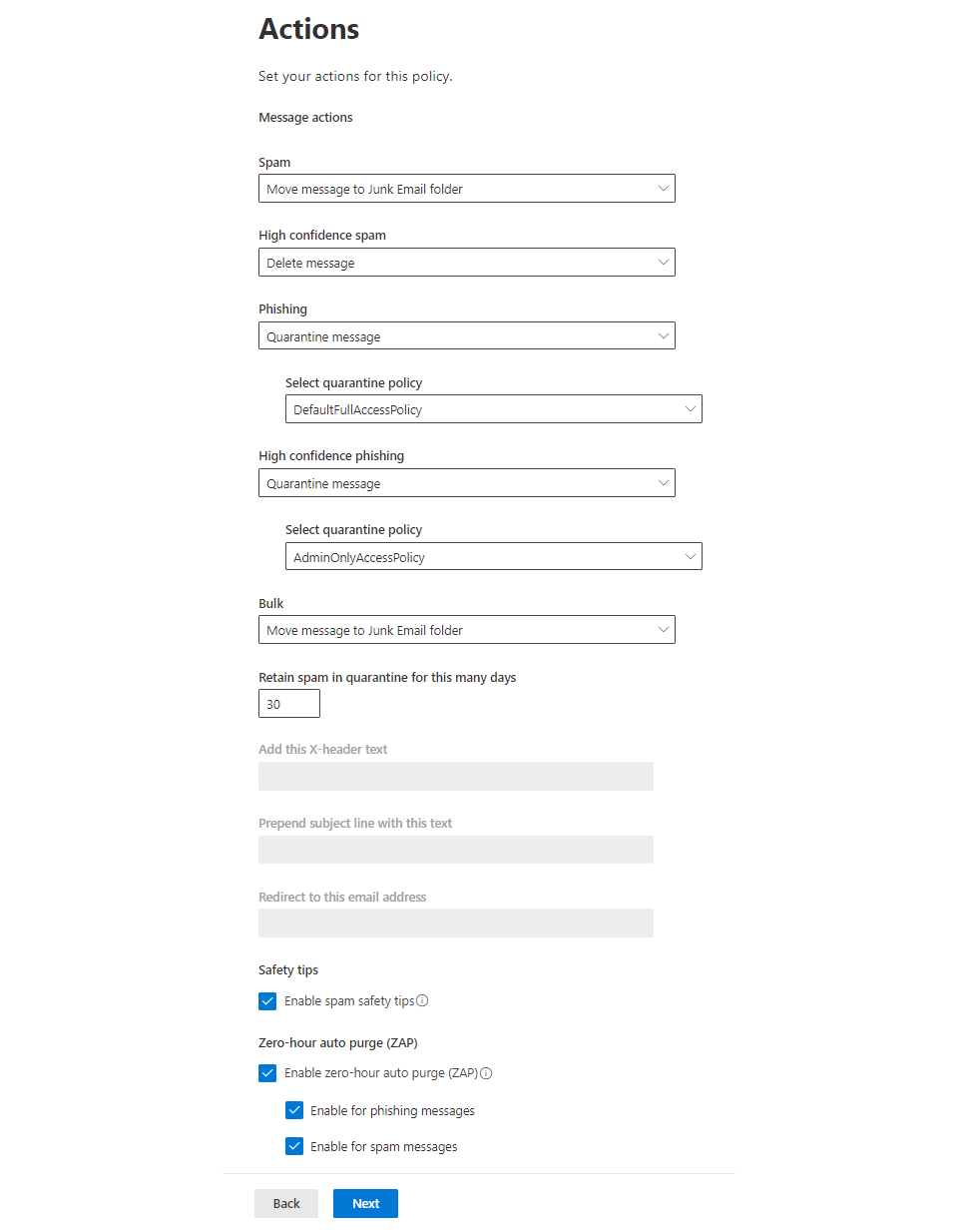
Then, we choose the action for the messages, which are confident to be spam, phishing or bulk. Possible to choose from:
- Move message to Junk Email folder
- Add X-header
- Prepend subject line with text
- Redirect message to email address
- Delete mesage
- Quarantine message
Safety tips will show in as disclaimer and can also help to warn users about potential unwanted messages. ZAP, zero-hour auto purge is another great function to be effective on mails, that have already been delivered.
(https://www.oceanleaf.ch/content/images/2022/01/df-o365-spam-actions.png)
Last, but not least we can define specifically allowed or blocked senders and domains. This could be beneficial to add a domain from a certain external collaboration organization.
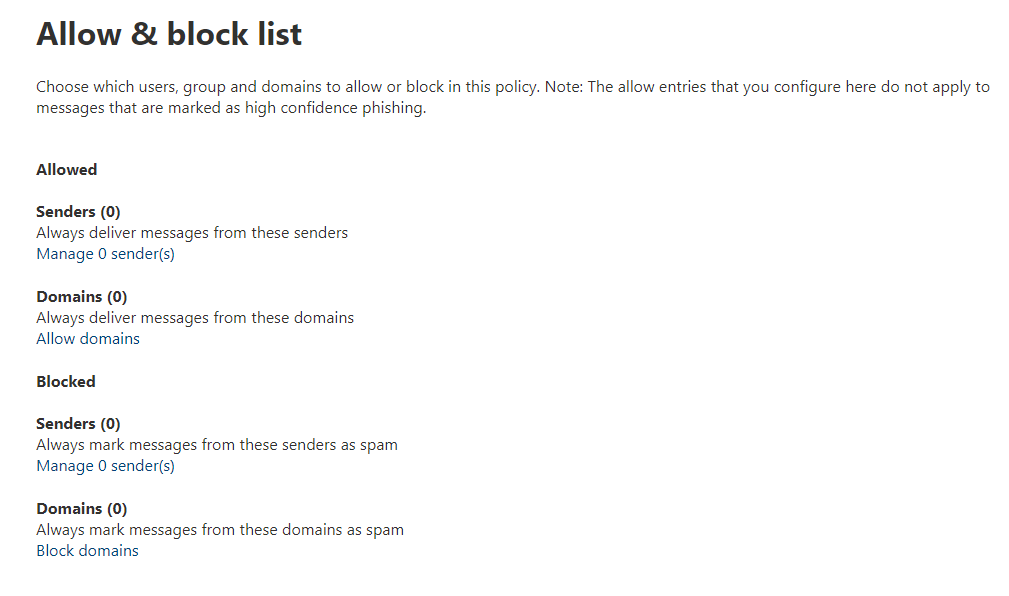
Review the policy and set it live.
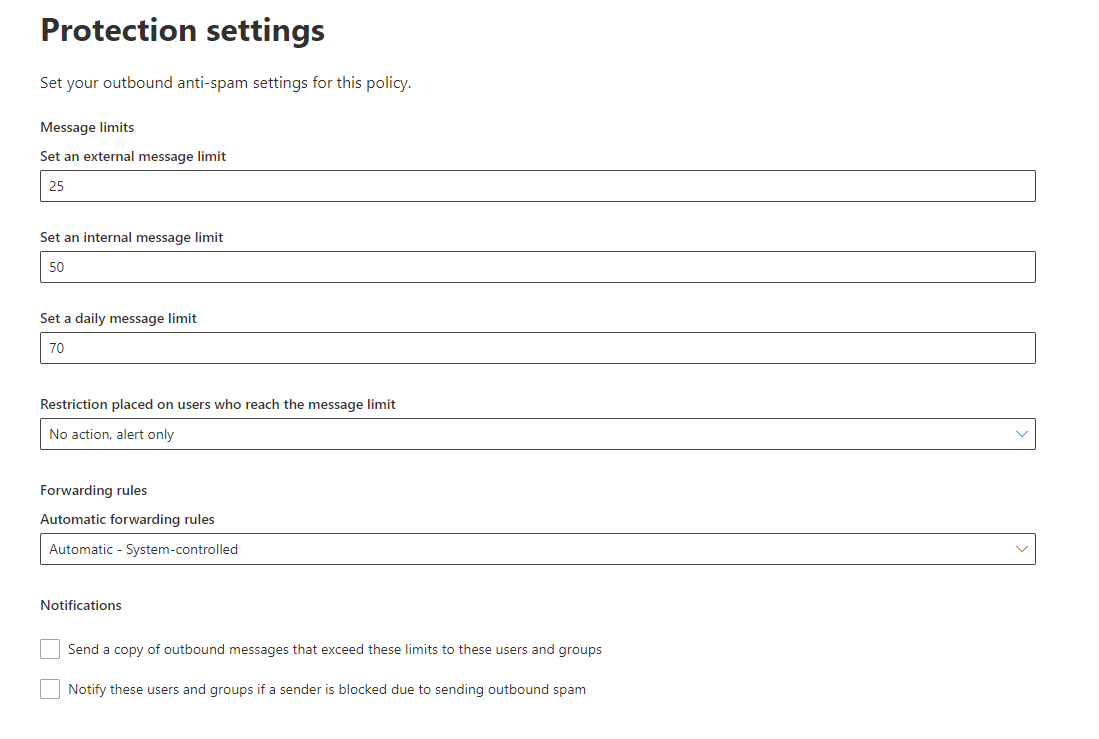
Outbound policy
In the outbound policy we mainly care about message limits for both directions. Subsequently the the restriction policy that would restrict the user from sending mail or alert only. The automatic forwarding rule is in charge of any rules that would forward a message automatically. Notifications can be enabled to inform administrators when the policy has been triggered.
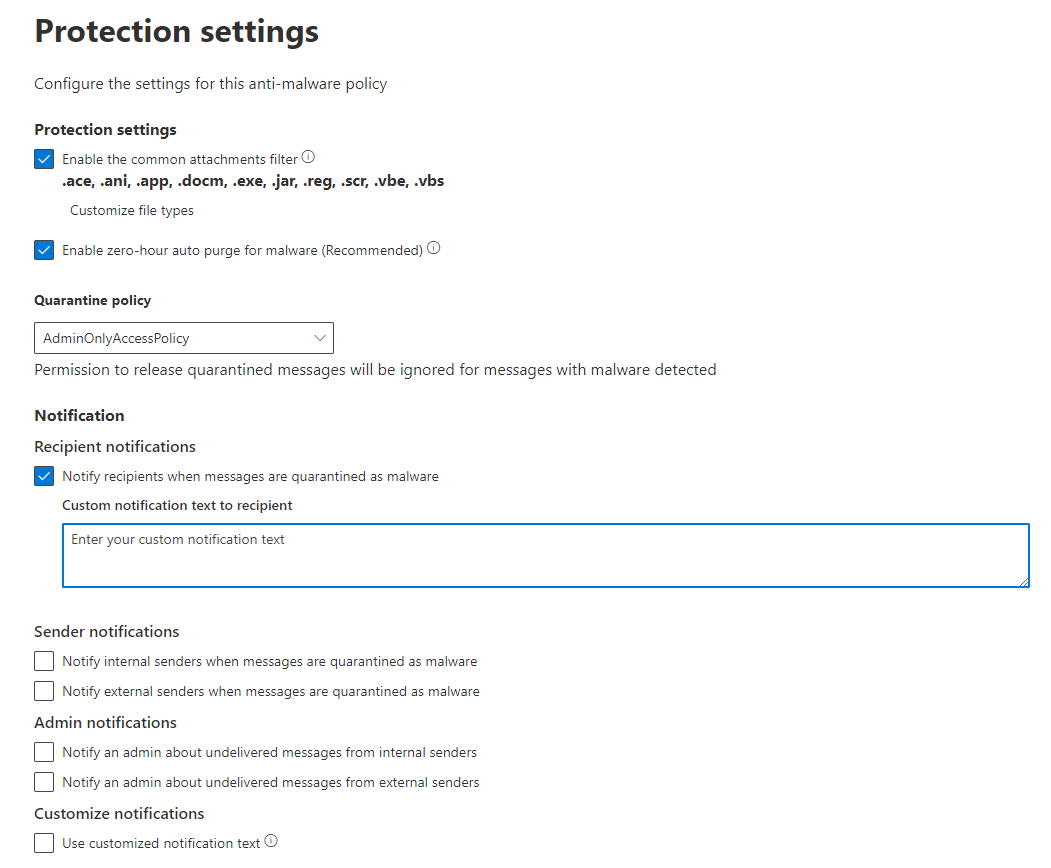
Anti-malware
Anti-malware detection works with an attachments filter, that has common file extensions/types included, which can be customized. I would definitely also enable ZAP for this feature. Next, the quarantine policy can be selected. (I will cover that later) And again, we have notification options for the internal/external sender, additionally admin notifications, if a message was undelivered because of malware.
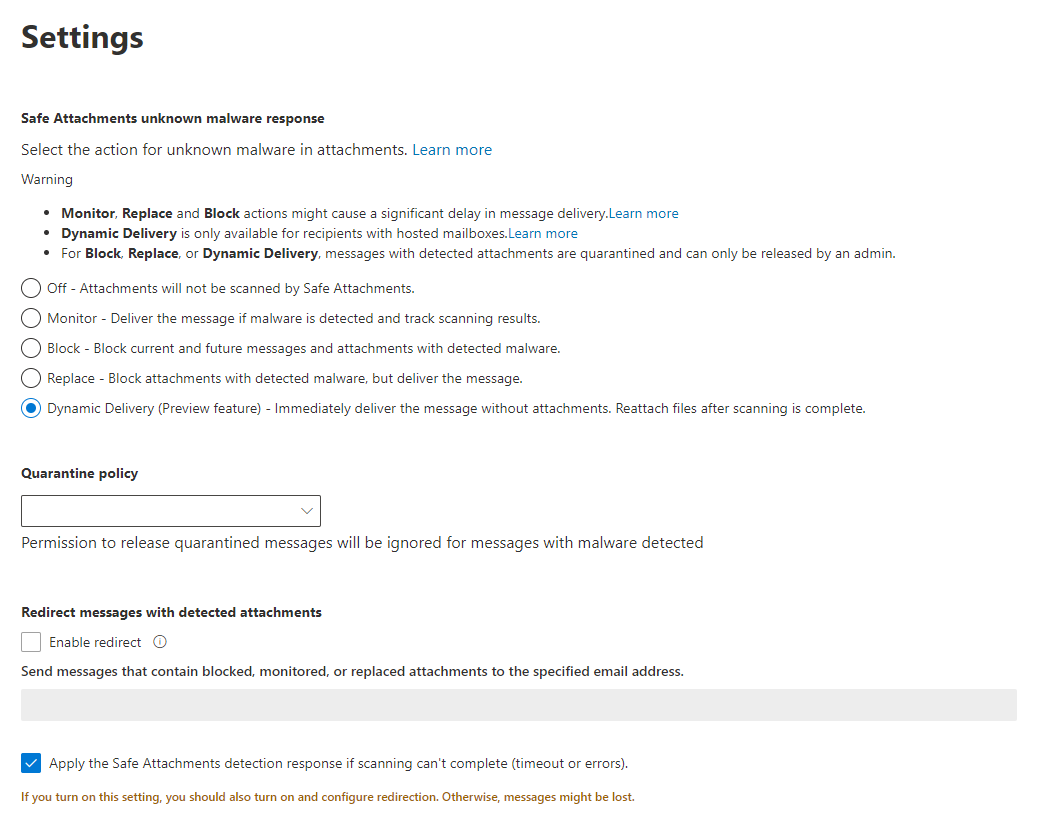
Safe Attachments
So Safe Attachment settings are about the behavior of attachments and can be set to:
- Off - no scanning
- Monitor - deliver the message anyway and track the scanning results
- Block - block messages that have detected malware attached
- Replace - block attachments, but deliver the message
- Dynamic Delivery - deliver the message without attachment, reattach the attachment when the scanning is complete/no malware was detected
Again, you select the quarantine policy. A redirect of blocked, monitored or replaced attachments to a secure address is also possible. This should especially be enabled for messages that had an error or timeout during the scanning.
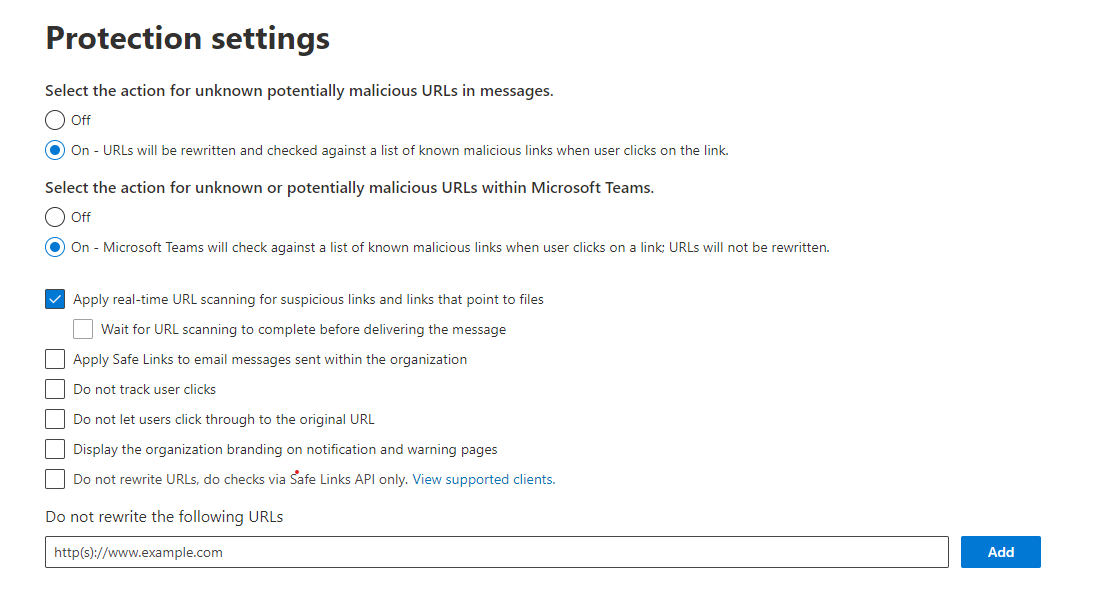
Safe Links
For the Safe Links feature, Defender will rewrite and analyze URLs in messages or Microsoft Teams. There are a couple of tweaks to this behavior and holds an option open to ignore certain URLs.
Rules
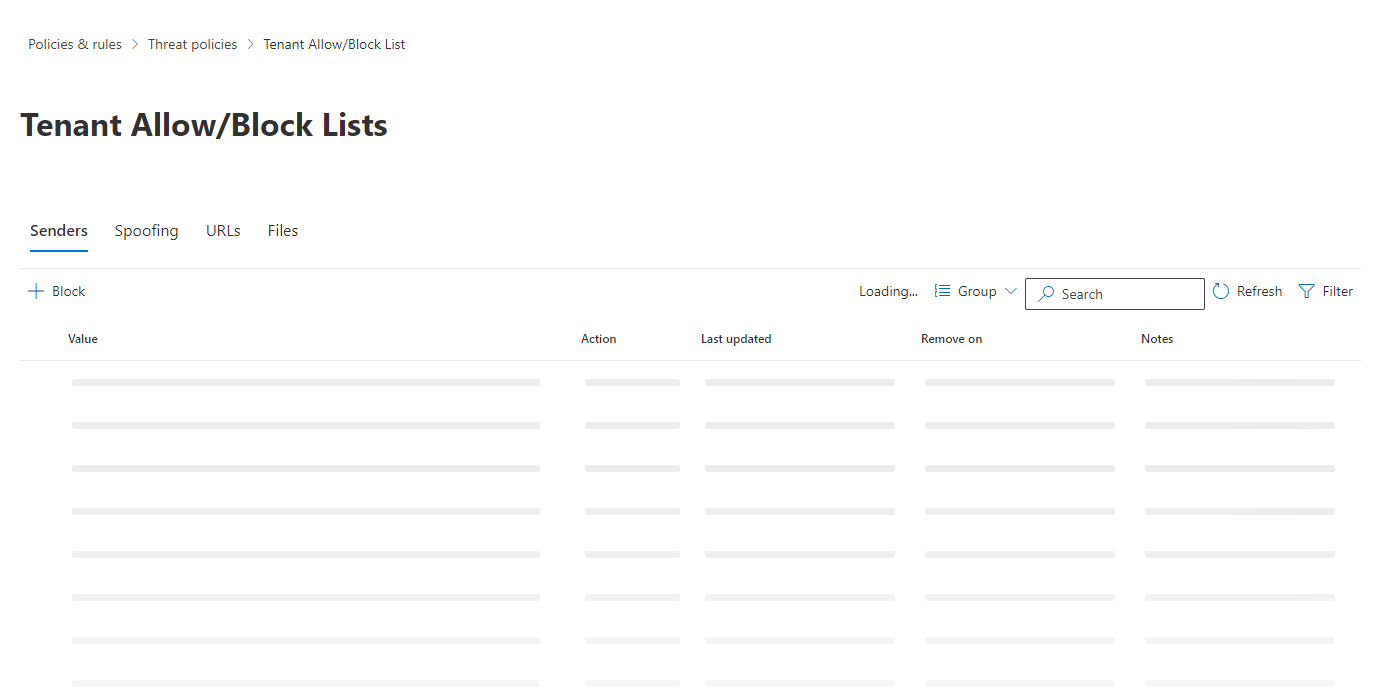
Tenant Allow/Block Lists
If there are any Senders (email addresses or domains), Spoofing (domains, IPs, users), URLs or Files (file hash) you want to allow or block explicitly, then you could do that here.
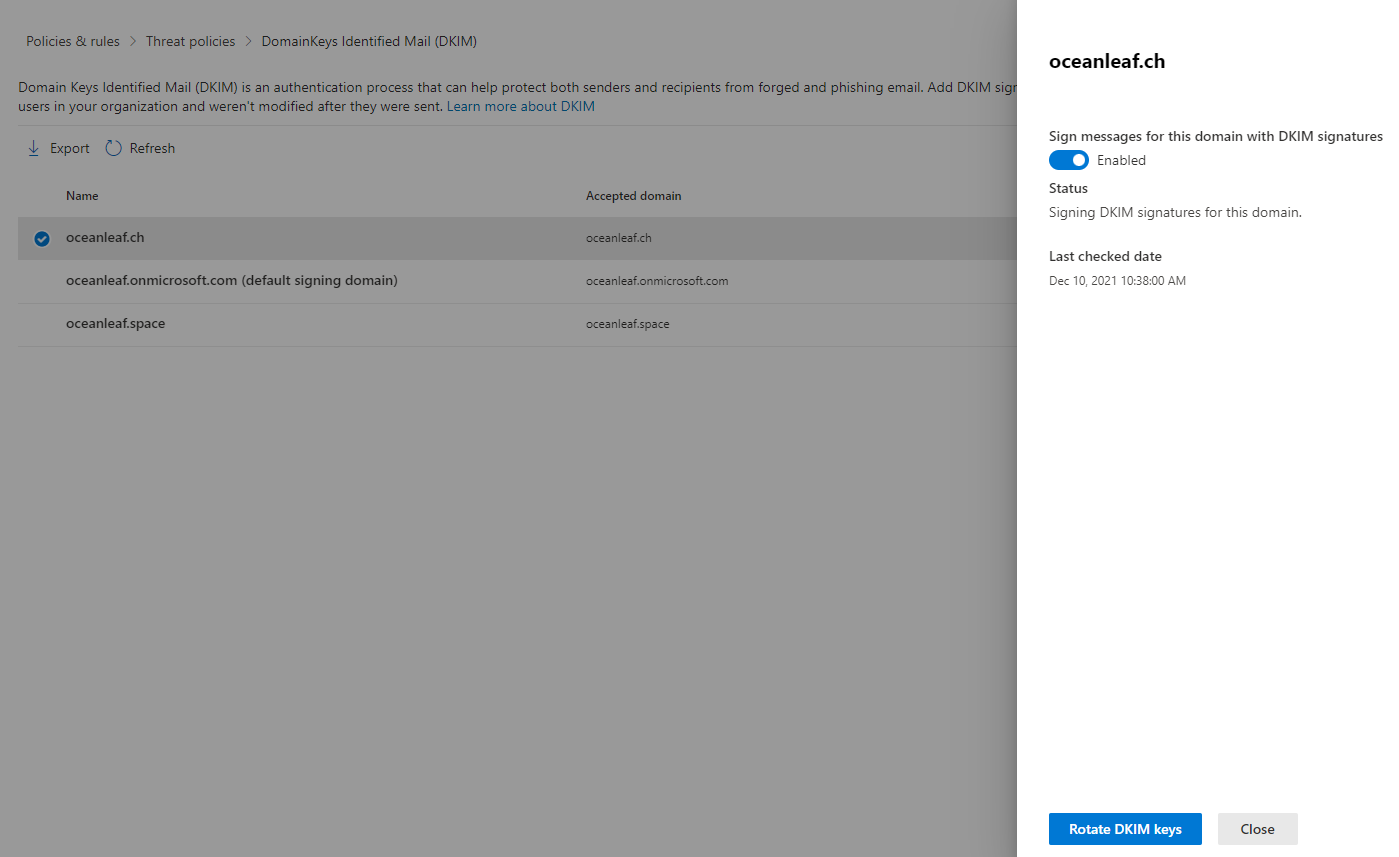
DKIM
Domain Keys Identified Mails signs the mail header and the message with a keypair to ensure, mails are not tampered in transit. This is tied to the domain. Though, a DNS txt record is required to store the public keypair. Just after enabling the option, the record will get displayed and must be added at the DNS hosting to your domain.
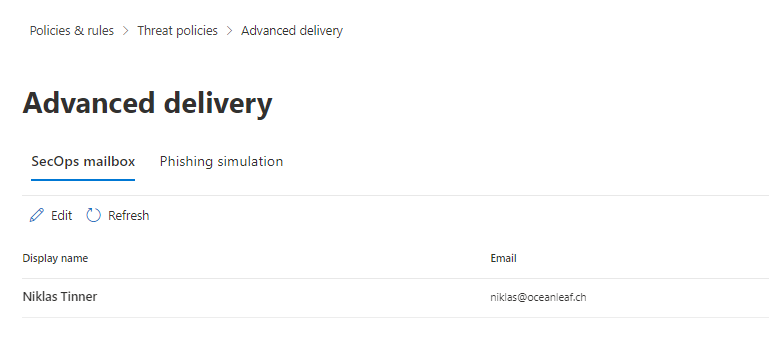
Advanced delivery
Advanced delivery allows message forwarding to a SecOps mailbox for analysis and investigation and additionally can be used to oversteer controls for a third-party phishing simulation tools.
Enhanced filtering
Enhanced filtering applies filters to connectors.
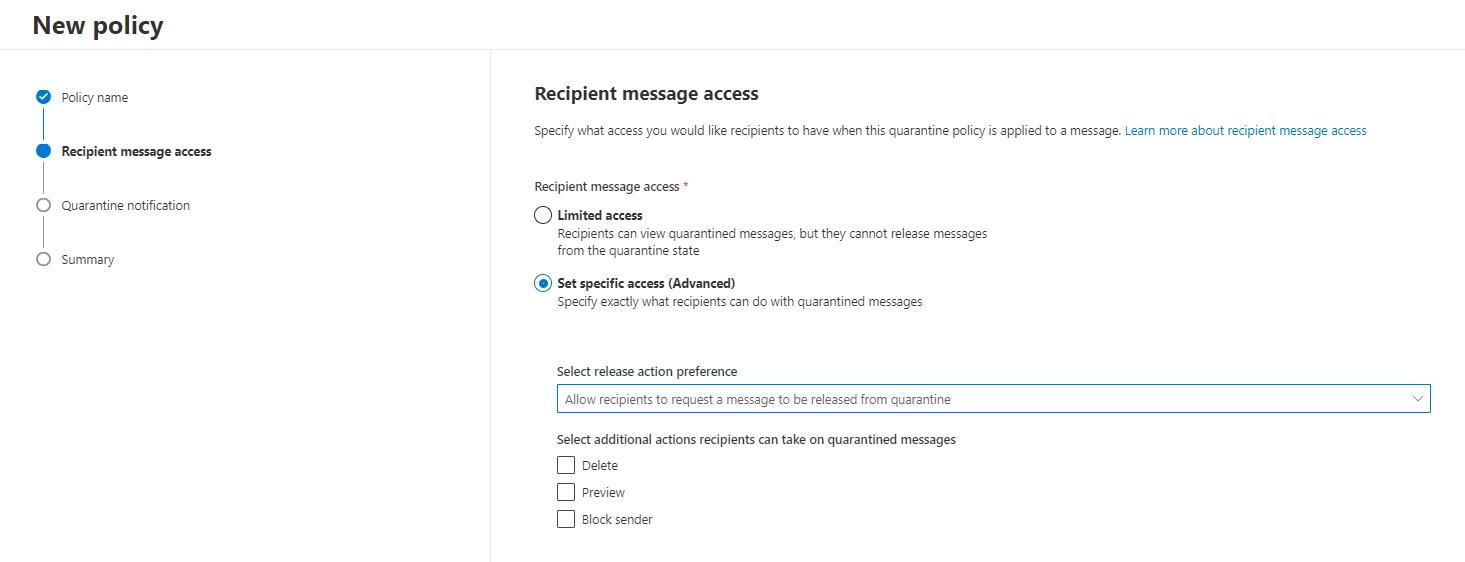
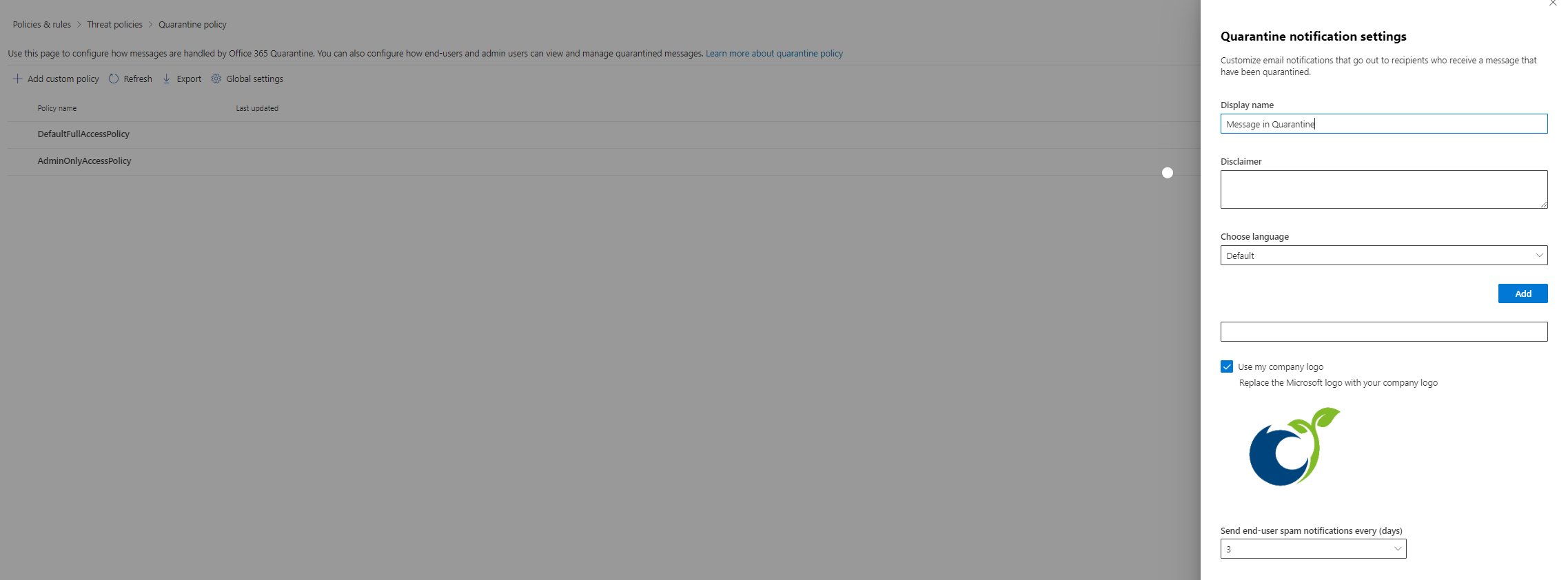
Quarantine policies
A quarantine policy is set to inform users or admins about quarantined messages. Essentially the permissions of actions to quarantined mails and their notification (known as digest) can be preconfigured. By default there are two policies:
- DefaultFullAccessPolicy, no notification, Full access to the end-user (https://security.microsoft.com/quarantine)
- AdminOnlyAccessPolicy, no notification, access to admins only
And there is a global setting to customize the notification message and its sending period:
Others
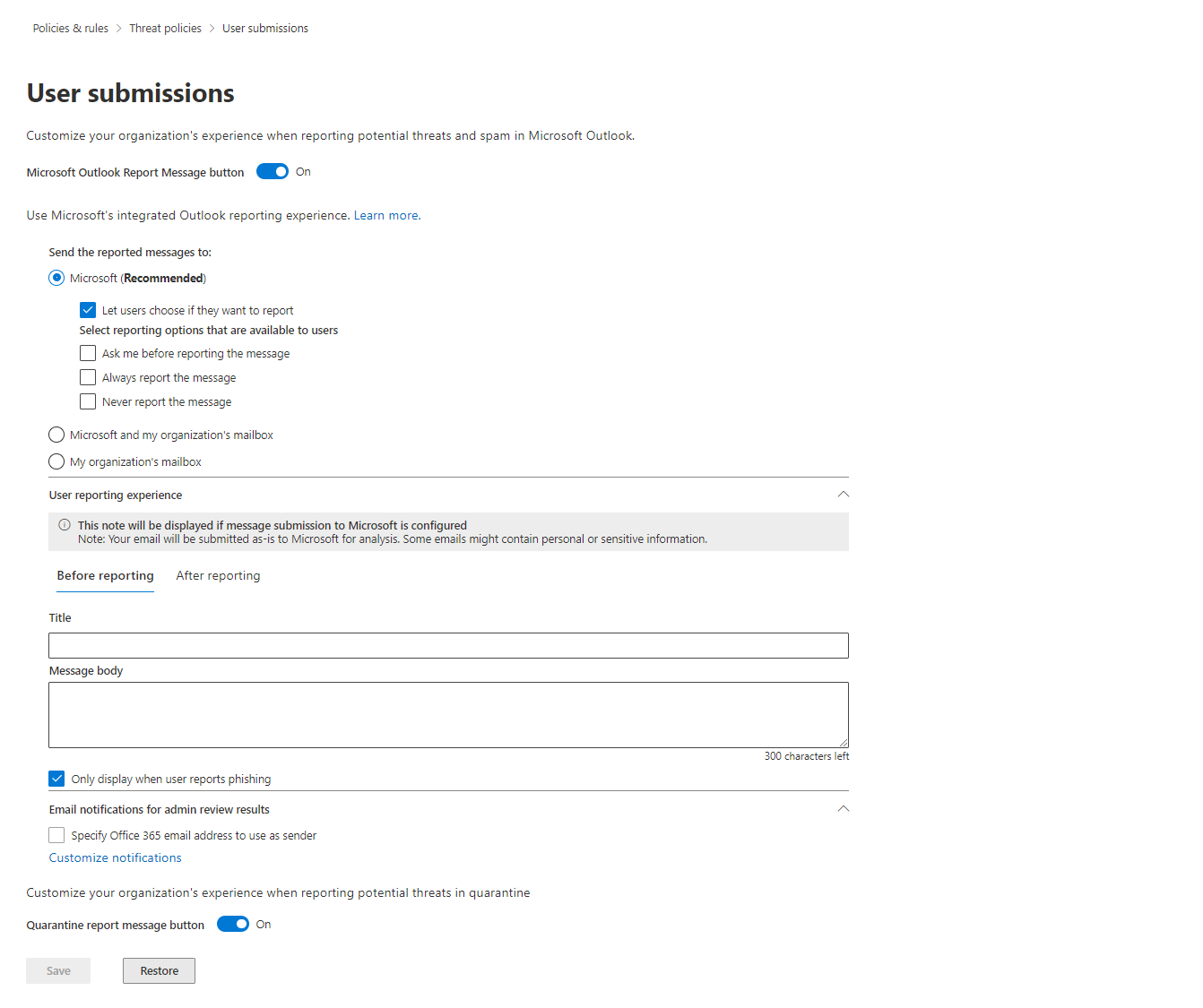
User reported message settings
When a user receives a message that they consider to be spam or phising, a submission action can be initialized. You decide if those messages are reported and sent to Microsoft or an organizations mailbox. Moreover the experience of such an action can be adjusted with an individual text. A little further down, you can see another notification setting, to customize the text when an admin confirms a message as phishing, junk or if they where harmless.
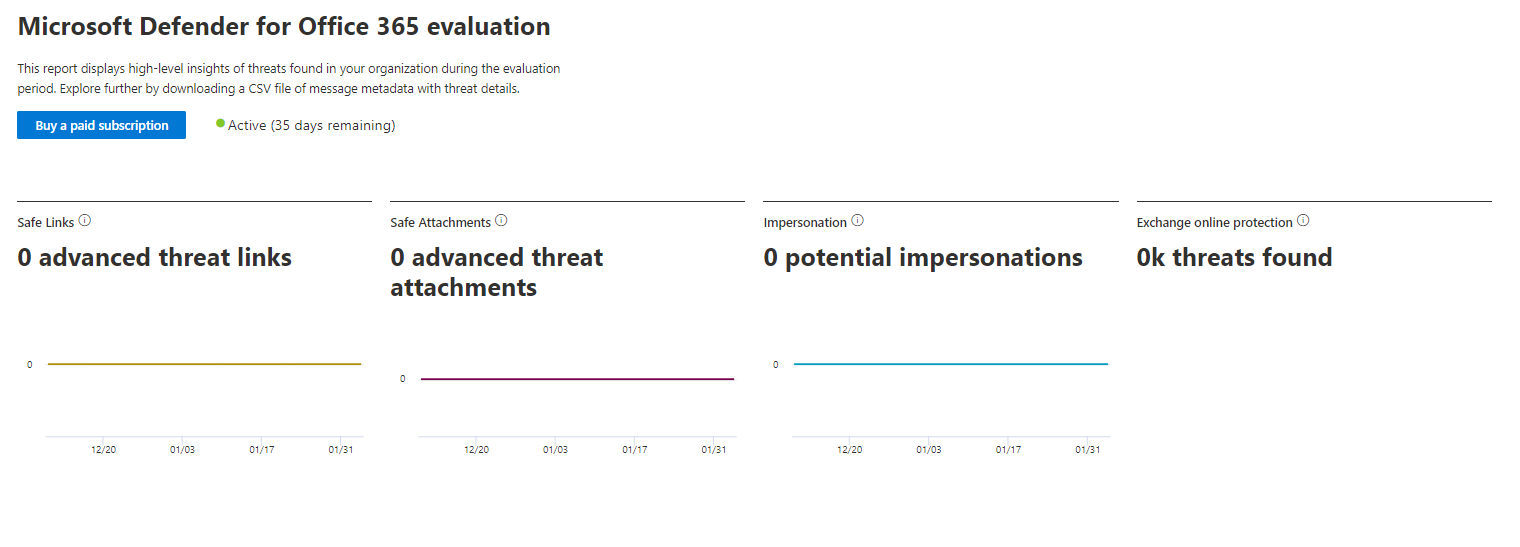
Evaluation mode
The evaluation mode holds an insight to EOP policies and operations to evaluate Defender for Office 365. In the settings you can even designate that you are using another mail protection product and its connector. More about it
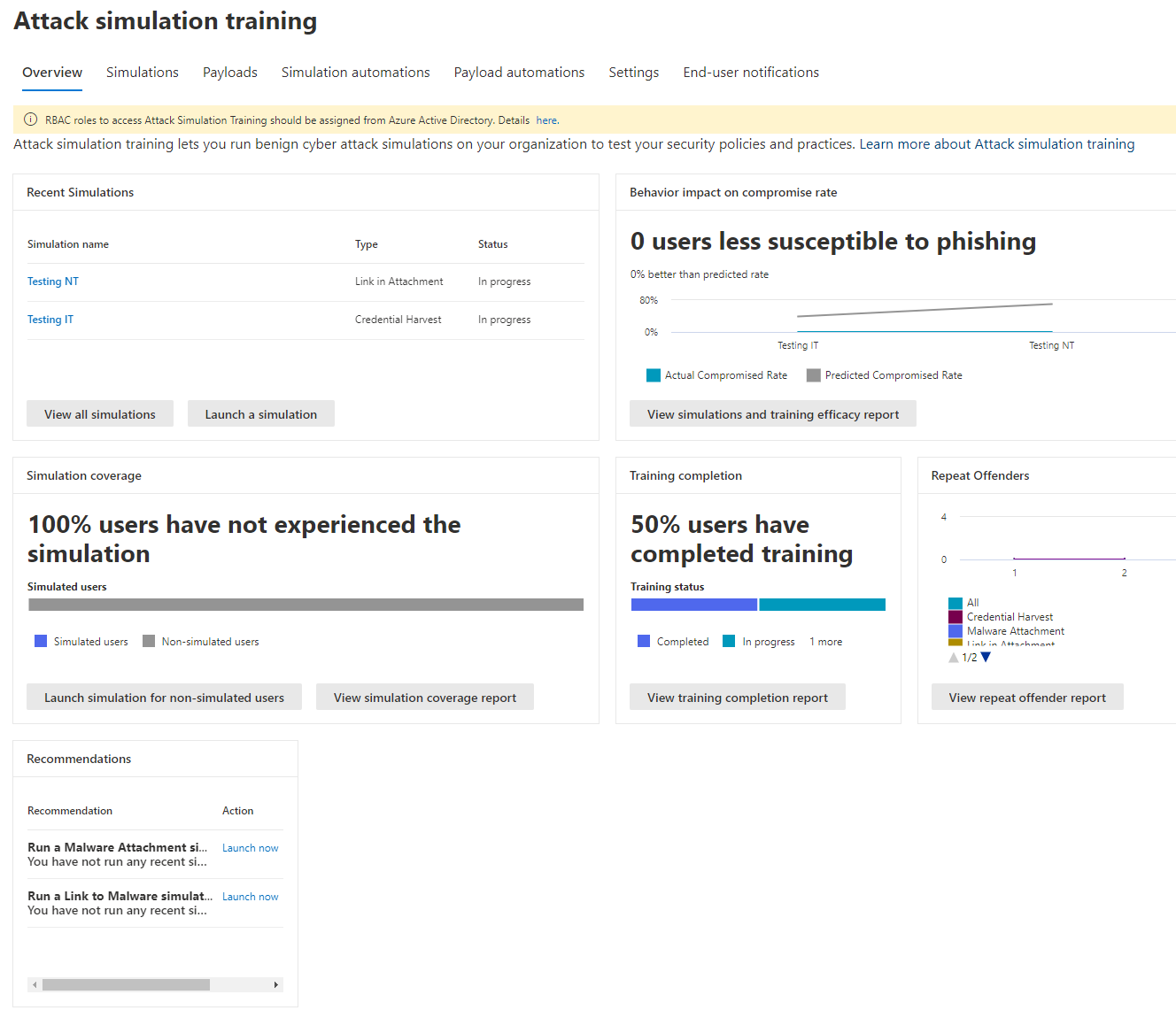
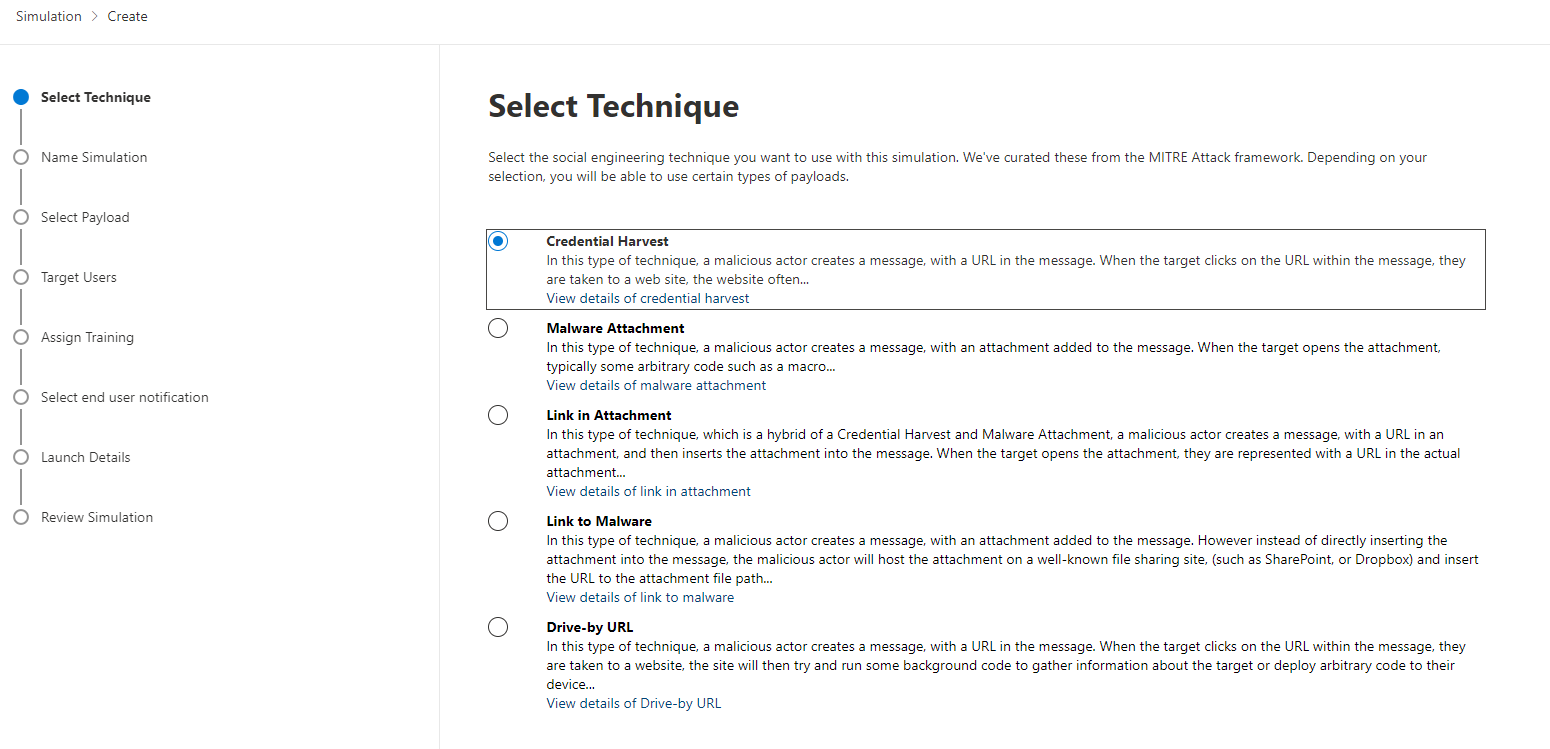
Configuration - Attack simulation training
Apart from all the technical measurements, we should focus on what is probably the weakest link in the chain: the user. If a malicious message is delivered and the user follows the request, everything we have configured will be for nothing. Though, the technical side does a great job most of the time, we can not guarantee that an advanced threat can bypass all the security controls. User awareness is the last and only defense at that point. Besides of awareness trainings to the employees, Microsoft provides an Attack Simulation Training in which a campaign can be launched to simulate an attack through multiple techniques to understand how your users deal with such a situation. Subsequently, based on their behavior (from deleting the email, reporting it, opening an URL or attachment, up to entering their credentials) you can schedule trainings that must be taken.
Investigation, Explorer, Threat tracker & Submissions
Threat Investigation utilizes automated investigation and response (AIR) capabilities to automatically remediate alerts and incidents, to safe time and effort. Official docs
The Explorer on the other hand gives insight to literally all delivered email actions across your tenant. From all mails, phishing, campaigns or content malware, you get statistics and detailed infos about all of them. Official docs
Campaigns provide an overview of all personalized attacks on an organization or Microsoft known (mostly new) attack patterns that have been applied. Official docs
Threat tracker is a more complex but deeper Explorer, that works with queries and campaigns to discover and track threats. Official docs
Now Submissions hold messages, URLs or attachments that are suspect, to report to Microsoft. It will then be reviewed and afterwards the results are sent to you. Official docs
Reports
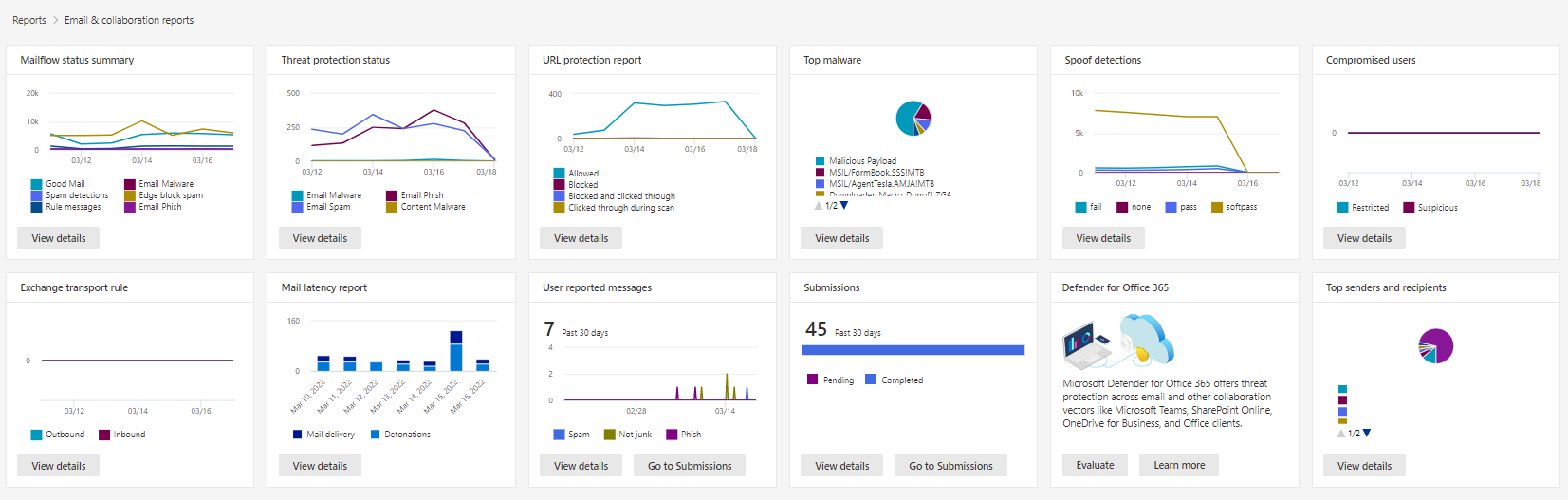
Reporting capabilities are found at the bottom section of Security Center and include powerful general, endpoint as well as email & collaboration reports. With "manage schedule" you can get periodical report summary sent to a mail adress. Furthermore downloading the reports is also possible.
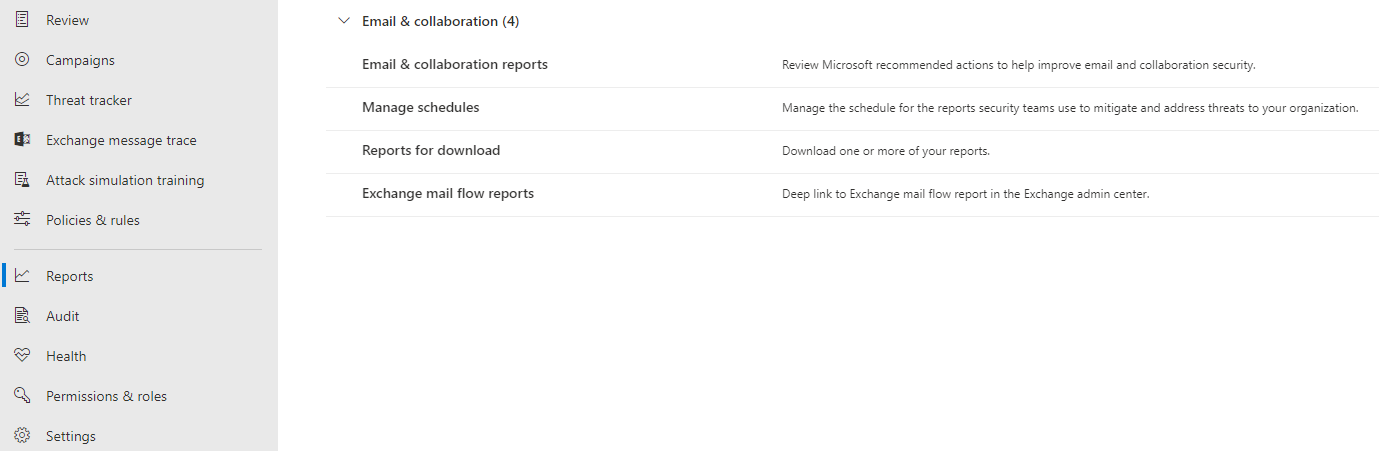
The built in reports include:
- Mailflow status summary
- Threat protection status
- URL protection report
- Top malware
- Spoof detections
- Compromised users
- Exchange transport rule
- Mail latency report
- User reported messages
- Submissions
- Defender for Office 365
- Top senders and recipients
Conclusion
This was the technical side of Microsoft Exchange Online Protection with Defender for Office 365. The product itself offers industry standard mail protection capabilities and is integrated to the Microsoft cloud ecosystem.
Mail protection core components are fully covered. But don't forget about crucial technologies like SPF, DKIM or DMARC.
From my experience a seamless switch from a third-part product to Defender for Office 365 is recommendable but must be planned ahead. End-user communication must also be done, especially to inform about the new quarantine types. Strict baseline policy is what I would go for because you will always have the security best-practices of Microsoft and don't need to care for individual policies. If you need exceptions, Exchange mail flow rules are usually to consider.
View all my Defender Suite contents
Read more about security topics on my blog