Microsoft Security
Microsoft security concepts
Learn about Microsoft cloud security high-level concepts to secure your organization with Microsoft 365 and Azure built-in products and features. The way to secure your digital assets such as identities, infrastructures, platforms, apps and data. These are the official Microsoft security sources. On my blog you can find two security

Microsoft Cloud Security: Top 10 low-hanging fruits
Introduction Almost every modern organization, regardless of startup or established enterprise has Microsoft 365 or Azure services in place to fulfill IT requirements and operations. The most common services include: * Microsoft 365 Apps (Teams, Outlook, Office etc.) for collaboration * Entra ID for the user accounts, identity (resources) * Azure platform hosting

Microsoft 365
Launch with Microsoft 365: a guide
Launch your business with Microsoft 365. Increase productivity, run and manage workloads, gurantee security & compliance.

Microsoft 365 Cloud Security correlation
If you ask me, Microsoft’s biggest advance and unique selling point in terms of security is the diversity of their feature offerings tied to the non-security products and the correlation between them. Always backed by the ability to retrieve all kinds of data from the past or in real time,

Security Reports in M365
This blog post is about reports from Microsoft 365 Security also known as Microsoft 365 Defender. As a prerequisite, one or, in the best case, several Defender products should be set up. The objective My initial objective was to obtain a high-level management summary of our Microsoft Defender cloud environment,
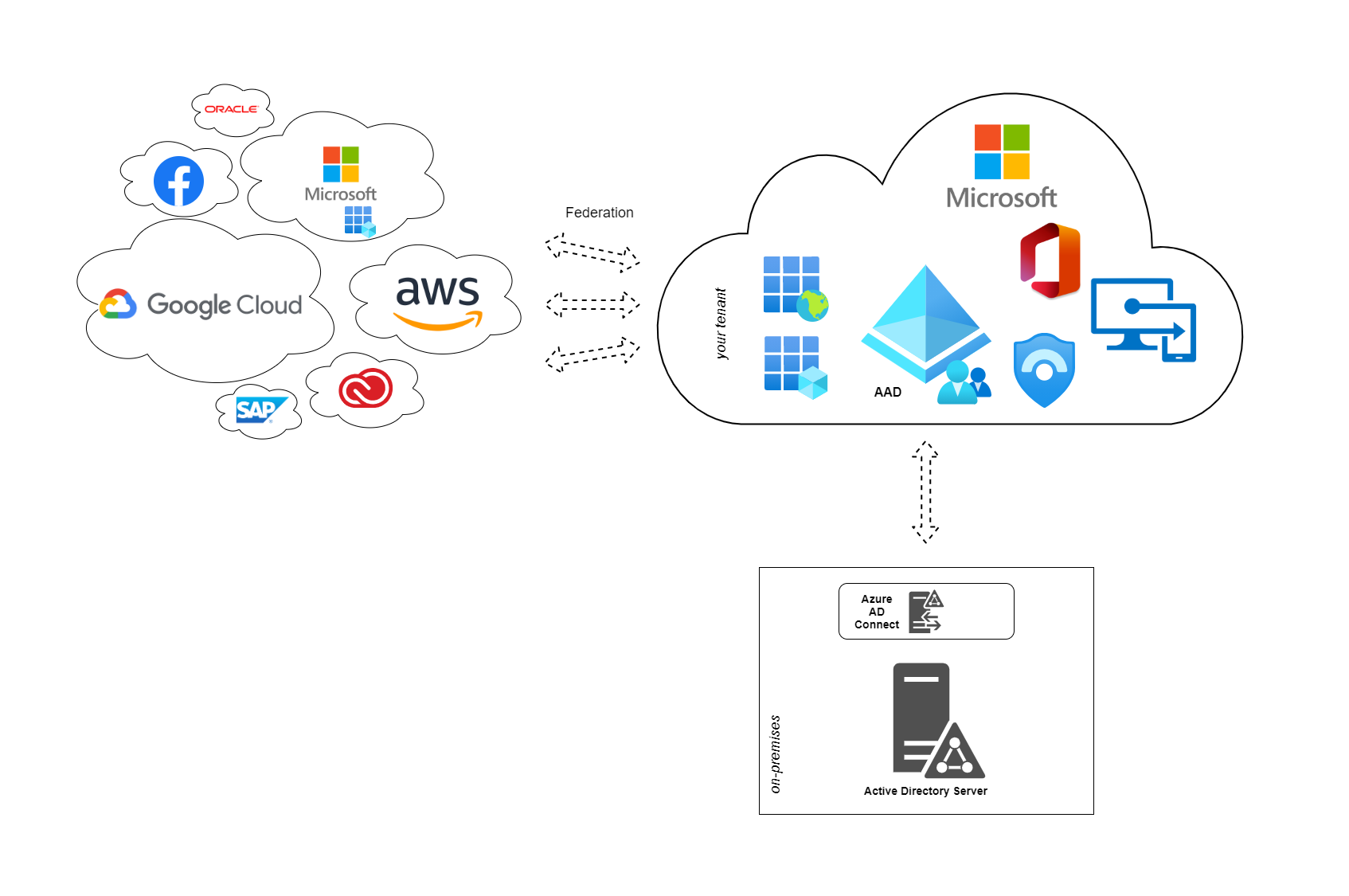
Understanding identity federation and application management in Entra ID
Information technology applications are moving to the public cloud. We call this SaaS software as a service, that rely on a multi-tenancy architecture and provide the same instance of a software to multiple customers or users.
Identity and Access Management
Conditional Access - The ultimate starter guide
Introduction In today’s world, workforce is more distributed and the security landscape keeps evolving. For IT security, identities and access management this brings some challenges along. A sign-in from a remote location, device or app may be suspect or originates from an attacker. However, we need to differentiate between legit

Microsoft Entra Security Service Edge
Introduction to Microsoft Entra Security Service Edge (SSE)
Introduction New Microsoft technology was released! Microsoft recently announced Microsoft Entra Security Service Edge. I want to briefly summarize whats new as part of my learning. 💡At this time these features are in an early stage and most of it is in public/private preview. SASE The concept of Secure


