What you need to know about Intune
Managing devices from the cloud may first sound a little strange and complex, but it's not! Microsoft Intune helps creating a lite- to zero-touch deployment called "Autopilot" for a machine across multiple operating systems. Have you ever wondered how this exactly works? Well this will then help you to get a rough idea of whats possible:
So whats Intune?
Intune is part of Azure which is defined as all cloud products offered by Microsoft. It is an MDM (mobile device management), part of EMM (Enterprise Mobility management). Reachable through https://devicemanagement.microsoft.com/. Following components are part of this portal: Devices (Enrollment, but also configuration tools), Apps (including app policies), Endpoint Security, Reports and Users/Groups which comes through AzureAD. There are some prerequisites to start using this technology, read my article where I lose some more words about the technical aspects.
Content of this blog will be:
- Device enrollment
- ESP
- Deployment Profile
- Devices
- Device configuration
- Device configuration profiles
- Powershell scripts
- Device updates
- Windows 10 update rings
- Windows 10 feature updates
- Apps
- Integrated apps
- Win32 apps
- Windows Store apps
-
- Endpoint Security
- Baselines
- Antivirus, Disk encryption, Firewall
- Attack surface reduction (ASR)
- Endpoint Security
- Compliance
Living in the jungle of Microsoft services
I think I don't have to tell you that Microsoft has a good amount of Cloud solutions/services. This is really what I personally love. There is so much for every direction, no matter it's Enterprise Mobility, Office, Security with it's concepts (IAM, Threat Protection, Information Protection, Security Management), management tools and so on. Provided on IaaS, PaaS and Saas - there is a service for everything that you have ever dreamed of. And in this jungle (positive meant) there is real life. These services can interact with each other exchaning information which is wonderful, combining them will make you almost invincible.
Licensing
First off, let's take a look to the licensing model for Intune. Don't worry we will just get a rough idea what to consider. So as I already wrote Intune relates to EMM that corresponding licensing is EMS E3 or E5 (Microsoft Enterprise Mobility + Security). EMS E3 costs under 10$/month that should not be an obstacle.
How an enrollment works
If we take the most simple scenario which is AzureAD join without any preprovisioning, an enrollment would look like this:

- Every device has a unique hardware hash. This has to be assigned to your Microsoft tenant, so the device knows (or is permitted) to join the organization. This can be done by your hardware vendor or manually with a script from Michael Niehaus that has to run on the device.
- The Windows 10 device arrives at your place with OOBE (out of the box experience, remember where you set langauge, keyboard layout privacy and so on). From there you login with organization credentials. (the device already knows that it is owned by the organization)
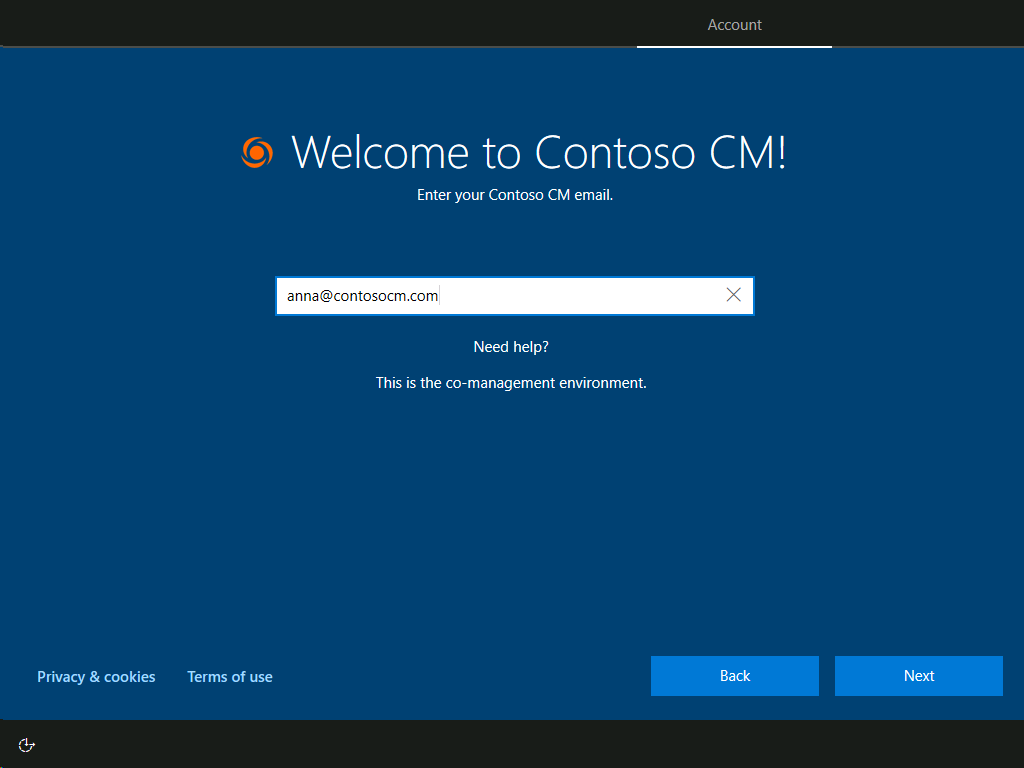
- After successfull login an ESP (enrollment status page) will occur, that shows the status of the enrollment with all information the device needs to apply. e.g. polcies, security profiles, apps that are targeted to either the device or the user. But this is also the point where the device enrolles into Intune and creates an AzureAD object.
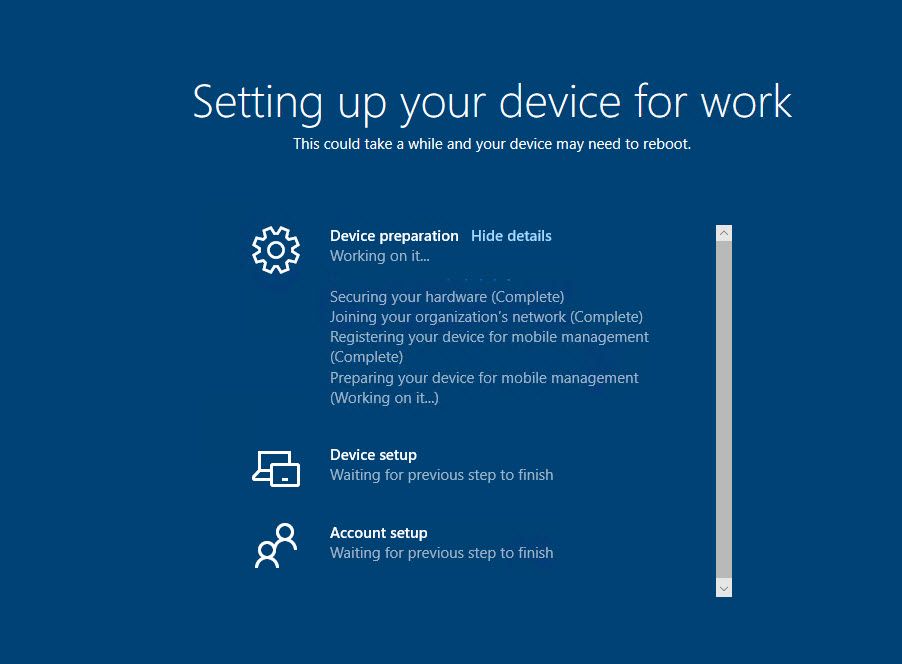
- From my experience this usually takes around 30 minutes. Then the device is basically in a business ready state within Windows 10. If you are experiencing issues in here or even recieve a red error screen, take a look to my troubleshooting article.
Ok, thats the process! Easy, isn't it? But now, how do take the settings?
Device enrollment settings

This is an image of all you can set for enrollment settings. Important is that
Intune is registered as MDM automatic enrollment.
ESP configuration:
ESP can be adjusted with the following settings. Pretty straight forward.

Deployment Profile
This is where it gets a little more interesting. Especially selecting the scenario AzureAD/Hybrid is where the real opportunities offer (remind that Hybrid scenario will need an Intune Connector, local installed on one of your servers). One thing that is also practicable is the self-deploying mode that is currently in preview. With this there is barely no user-interaction to enroll the device. (only for AzureAD)

Devices
All the assigned devices show up here. (by hardware hash)

Device configuration
Configuration profiles
One way to administrate the endpoints are configuration profiles. This is familiar to GPO's (group policies), just in a more cleaned up way. And to what I have seen I would say that these settings cover about 70%-80% of the GPO options. And if this is not enoguh you can always go for the OMA-URI path to the GPO path.

Powershell scripts
Sometimes a Powershell script can be really helpful, that you upload. But keep in mind that this borders on negligence because these scripts only run once on a machine and are hard to adjust and reapply in the future.
Device updates
Windows update rings
Controlling the updates on endpoints can also be done through Intune. This functionality is provided in update rings. For best practice use multiple rings for IT, pilot users and the whole company. You define the servicing channel and how it behaves for the machine and the end user. One hint; if the pilot users encounter problems with newer versions or updates, you simply pause the quality or feature updates for the company.

Windows feature updates
To target and install specific feature updates such as Windows 2004 use feature update profiles. Select the group of devices and the desired version and let it run. Sounds simple? Yes. To be honest I haven't tried this yet.
Apps
To integrate apps you have various options for all kind of apps. You can make it easy via. the Windows Store or have it with Win32 apps or line-of business apps. (which I haven't collected many information about)
Integrated apps
The most important applications for a common user are a Browser and Office, right? Well Microsoft delivers a Browser with their Chromium based Edge and Microsoft Office 365. Thats fairly easy to configure.
Win32 apps
Use Microsoft Win32 Content prep tool to create packages and trigger and cmd or ps1 file for the installation executable. We use Chocolatey as package service. Mainly that we do not encounter any problems with the updates. Read more about Chocolatey in my blog. This is really easy and reliable.

Windows Store apps
The Windows store is a great opportunity for many many apps. The only thing to do is to set up a connector between Intune and the Windows Store for Business. How to set it up
Endpoint Security
Baselines
Baseline offer a set of CIS and NIST conform policies that affect security on an endpoint. If you want to have it easy? Assign the baseline, but don't be surprised if half of the system is no longer fully functional after that. In August 2020 there are three baseline versions available.

Antivirus, Disk encryption, Firewall
I will also not write too much about this, because there are already many instructions around. Easy said:
Antivirus = configuring Microsoft Defender
Disk encryption = Bitlocker disk encryption & behaviour
Firewall = Defender Firewall
Attack surface reduction (ASR)
Here it gets complicated again. Attack surface reduction refers to hardening the system and have to control about whats going on in Windows. The baselines already have some settings from here included, nevertheless search the Internet for best practices or standardized templates from official institutes. In the end it is always about how much you wan't to invest in this and testing, testing and testing...
Compliance
The last on my list is compliance. Device compliance policies provide information about compliance state of a device that can be measured upon diffrent attributes. This should come from your organization compliance policies.

Please consider my full Endpoint Management with Intune path:


