Intune + driver update management - concept summary
Introduction
Here it is! Windows driver and firmware updates with Intune 🥳 This post will be a brief kick-off and concept summary of this new feature.
Previously, Windows Update for Business only allowed for a all-or-nothing setting. Driver updates could be blocked or allowed. Now we have the capability to monitor and deploy driver updates granularly and natively with Intune policies.
Official sources:
Components
- Windows Update (WU) - cloud service which is providing update sources through CDN
- Windows Update for Business Deployment Service (WUfB-DS) - another WU cloud service which provides control over the approval, scheduling, and safeguarding of updates to managed devices including an API and reporting
-> it identifies applicable driver updates for your devices from the WU inventory - Intune - configure driver update policies for enrolled devices
Features
- Let Microsoft automatically identify applicable driver updates for your devices
- Benefit from the trusted inventory of WU catalog where vendors and OEM's publish their drivers
- Approve, decline/pause updates
- Control visibility of optional updates
- Profit from detailed reporting within Intune
Prerequisites
| Category | Requirement |
|---|---|
| OS | Windows Pro/Enterprise/Education 10/11 (no LTSC support) |
| Licenses | Intune Plan 1 |
| Azure AD Free or higher | |
| Windows 10/11 Enterprise E3/A3, M365 Business Premium | |
| Device | Run supported Windows version |
| Enrolled in Intune and (Hybird) Azure AD joined | |
| Telemetry level of required (default) | |
| Microsoft Account Sign-In Assistant wlidsvc must be able to run | |
| Access network endpoints | |
| Intune | Don’t block driver updates in Windows update rings |
| Enable Windows data collection for reports |
Deployment strategy
Before you create the Intune profiles, you should think about the deployment strategy:
🛑 “Red button” – assumes all good until proven bad, IT admin explicitly stops manually
✅ Green button – assumes all bad until proven good, IT admin validates and pushes new content
Deployment rings
I would generally recommend to leverage multiple policies, to create a ring-based approach. This means that certain users/devices receive driver updates earlier to test their functionality and verify everything works as expected. If some negative impact is detected, the driver update can be paused for the current ring and declined for the later rings.
My recommendation is to create 1-4 update rings in which you add different device/user groups. If you go for automatic approval, make sure you add enough deferral time, the bigger the ring gets. For manual approval, you need to approve every single driver update. Both have advantage and disadvantage.
Membership approaches
To build the policies, you need to think about the memberships and the deployment rings. Multiple approaches possible:
- Same rings and deployment as from the Windows Update rings
- One policy per hardware model (Assign to all devices and make a filter on model)
- Build an automation to add differrent hardware models in a ring deployment
- Use Windows Autopatch
How it works
- In Intune you configure a profile and choose an approval method:
- Manually approve and deploy driver updates ⚒️
- Automatically approve all recommended driver updates 🚀
- Devices check-in to WU within 24 hours on their daily update scan and report to WUfB-DS and Intune
- Intune and WUfB-DS sync daily to process the data from the endpoints and show the results in the Intune admin center
- Either you approve a driver update or it gets automatically approved - this will tell the device to install the driver update silently on the next Windows update search
Automatic approval
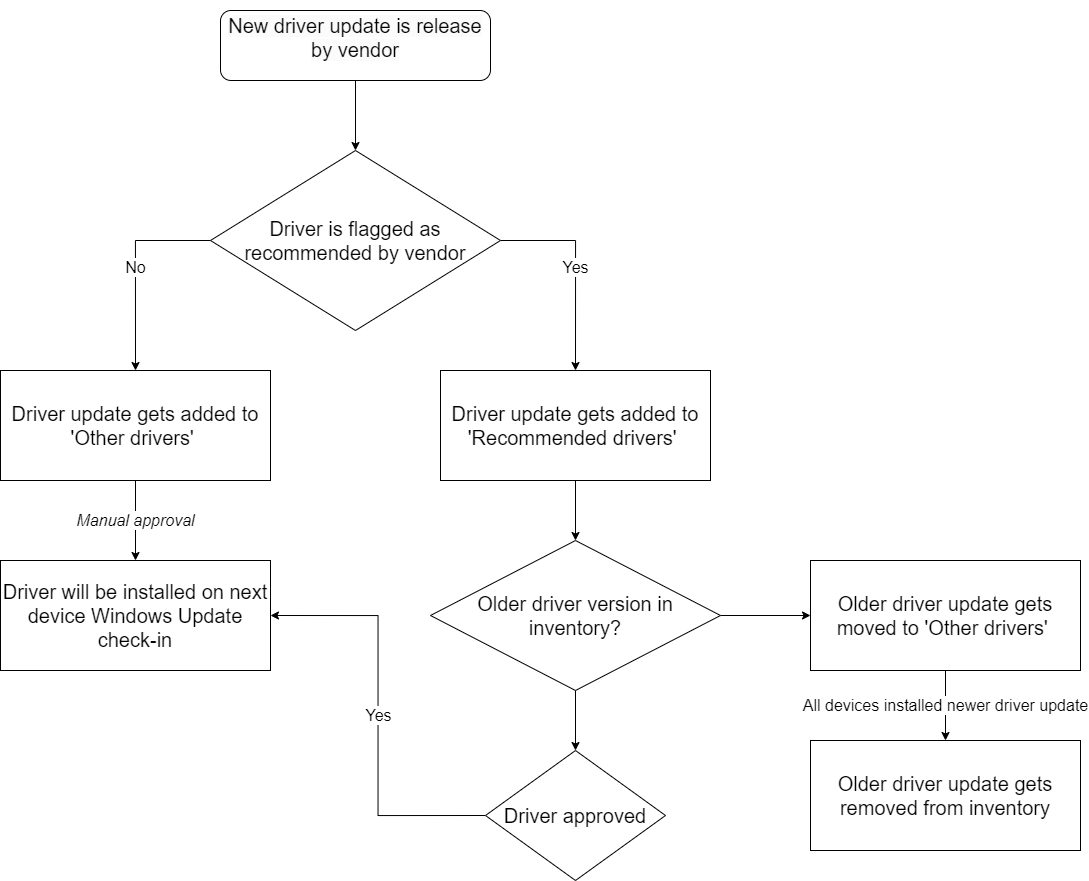
If you want to have fully automated workflow, you can consider to automatically approve all recommended driver updates. In short, the following process will take place continuously
- An independent hardware vendor or OEM marks a driver update as required or recommended
- WUfB-DS syncs the inventory to Intune for applicability checks on devices
- Driver updates are automatically approved
- On the next Windows Update scan (daily) the device will install that driver update
- As soon as a newer version of the update is released, the older version will get moved to the 'Other drivers' section
- The older version will get removed from the list in Intune as soon as all devices have the newer version installed
Driver update lifecycle
This flowchart shows the lifecycle of a driver update.
Setup
- Go to Intune admin center
- Navigate to Devices>Windows 10 and later updates>Driver updates
- Create a profile, name it and choose the approval method
- Assign to a group
- Regularly review and approve updates (if approval method is manual)
Opt-in to this new feature
Every organization who wants to start using the driver update feature with Intune, I advice to opt-in with the following steps:
- Get yourself an overview of your device types
- Plan deployment strategy and the rings
- Create one dev policy with manual approval mode and include some different device models (this allows you to get an idea of how much driver updates your devices would receive, without deploying anything. ⚠️ Once a driver update policy is assigned to a device, you stop the existing driver update deployment from WU only.)
- Create a policy for a limited amount of devices to opt-in to the feature (choose your approval method, I would start with automatic)
- Once you have collected your experience, prepare a general roll out concept and create more policies
Important notes
- Seach the Windows Update catalog
- Deadline and grace period settings apply from quality update settings
- Driver updates in Autopilot are not supported
- Roll back a driver update is not possible as of now
- Assigning a device to two driver update policies is not recommended (⚠️ status approved always wins)
- Firmware updates published in WU do not require the BIOS/UEFI to be unlocked
Looking for more contents on Windows Update (for Business) and Intune? Here you go: