Launch with Microsoft 365: a guide
Recently, I was faced with the situation of setting up a new Microsoft 365 tenant for my business use with Oceanleaf. It was very interesting to experience all the steps from the beginning. I think most of us will do this rather infrequently, so I want to give you some insight of a 2021 setup to it.
What is Microsoft 365?
Microsoft 365 and Azure are both clouds with hundreds of products & services that increase productivity, run and manage workloads, guarantee security & compliance and much more. Simply put, they deliver a remote service for all personal and business needs.
Start with Microsoft 365
Licenses
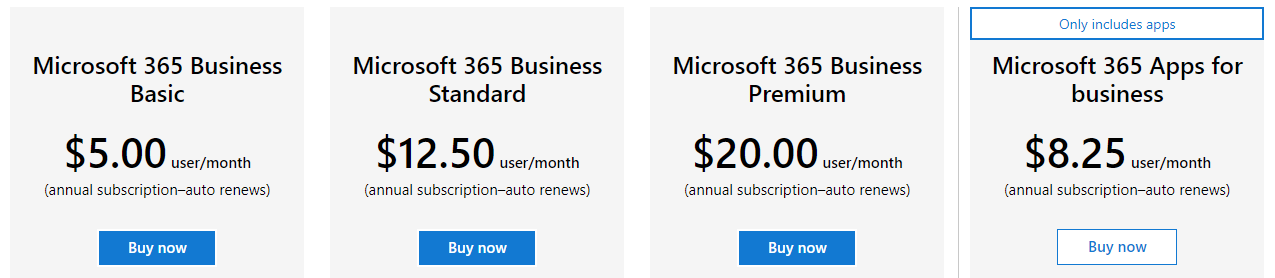
Initially we should take a look at the business service plans. Microsoft differentiates between Personal/home, Business or Enterprise. For small and medium-sized enterprises we are focusing on Microsoft 365 Business.
The business basic plan is the cheapest, but also the most cost-effective plan. You pay 5$/user/month and get all Office products online (without desktop version). Additionally there are 5 terabytes of OneDrive cloud storage. Thats really attractive in my view.
Sign-up
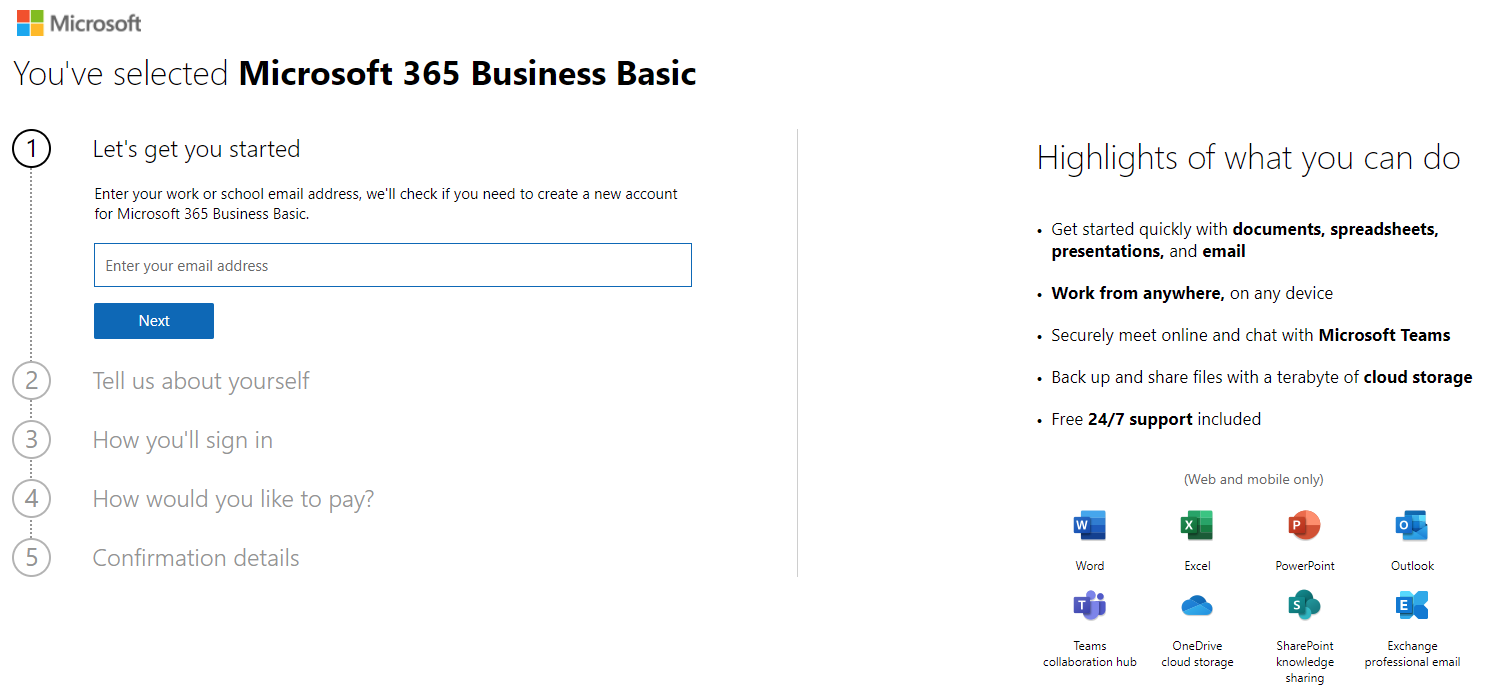
Choose a plan and prepare to enter some information about you and your organization. This is also where you specify the payment method.
Let's go
Basically, these were all steps to fulfill, to register and get started with the Microsoft tenant. I like that - just the necessary information provided and already good to start and use Microsoft 365 products & services for any needs.
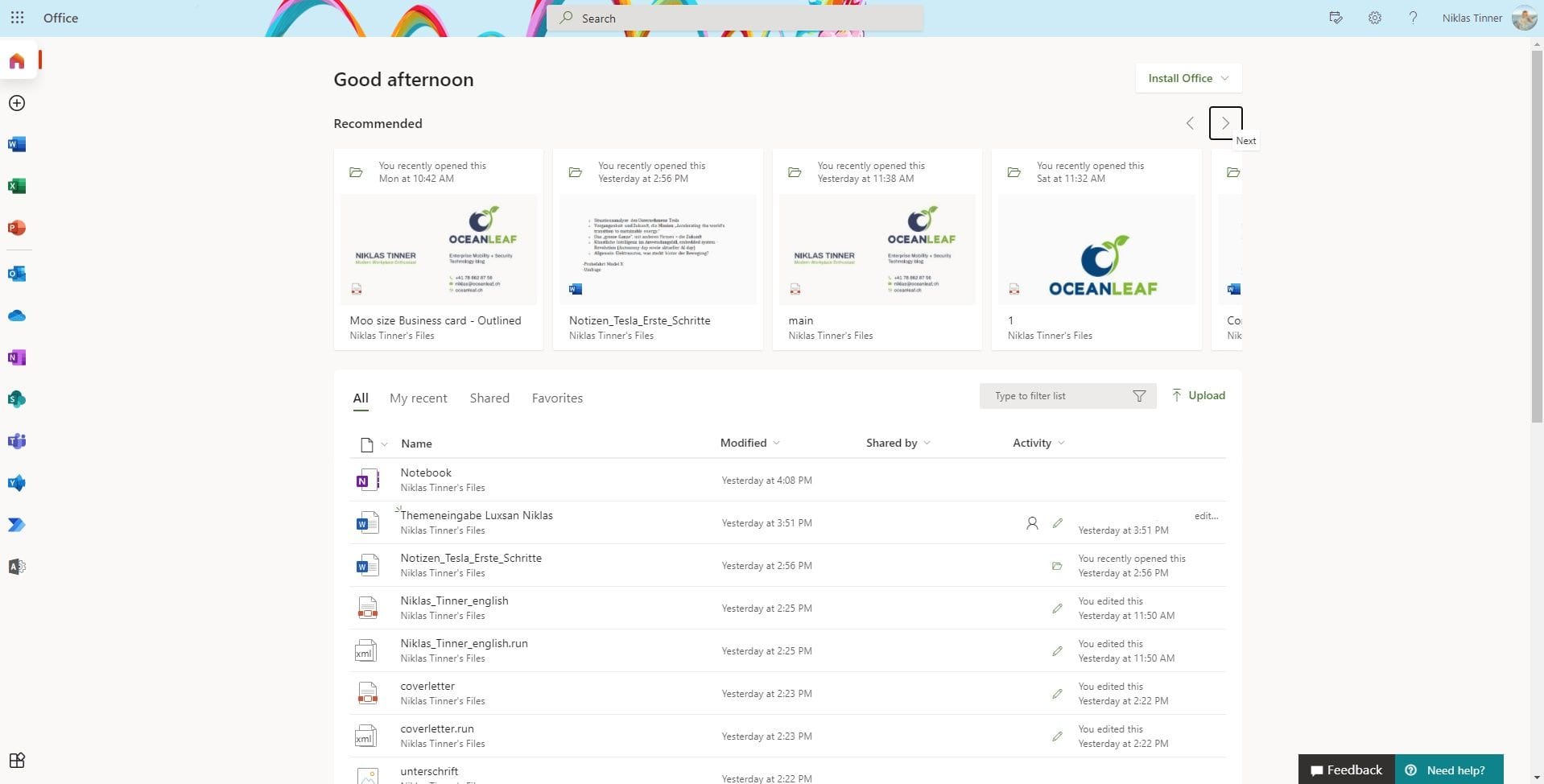
Now you either land in the:
- Office portal is where the user has access to all Office 365 apps such as Outlook, Word, Excel, Teams, SharePoint, OneNote, OneDrive and corresponding data.
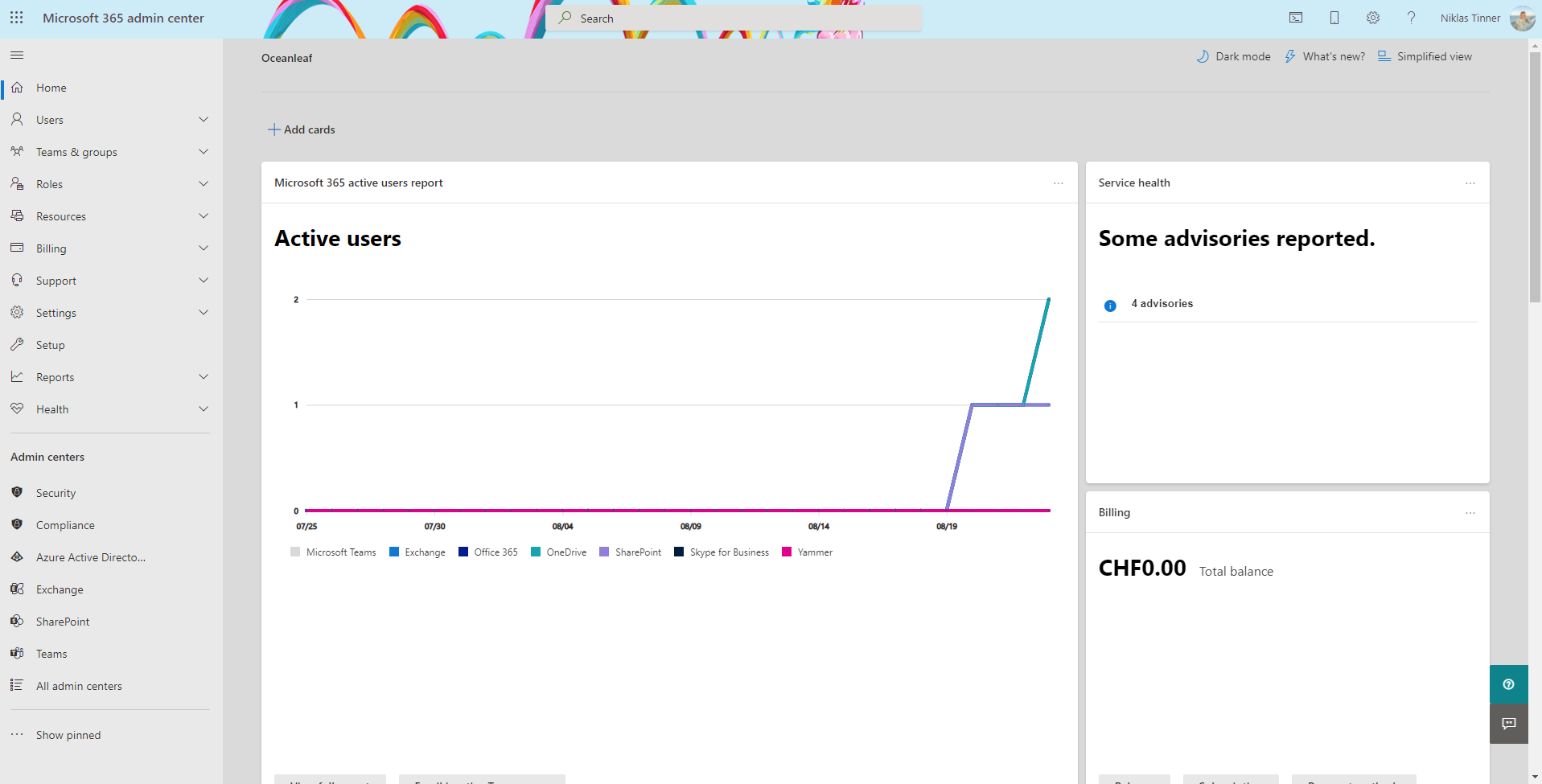
- Microsoft 365 admin center provides IT admins a single-pane of glass experience for managing all organization settings, such as user's and group's, global configuration, policies, branding and so on.
Configurations
Data location & organization settings (branding)
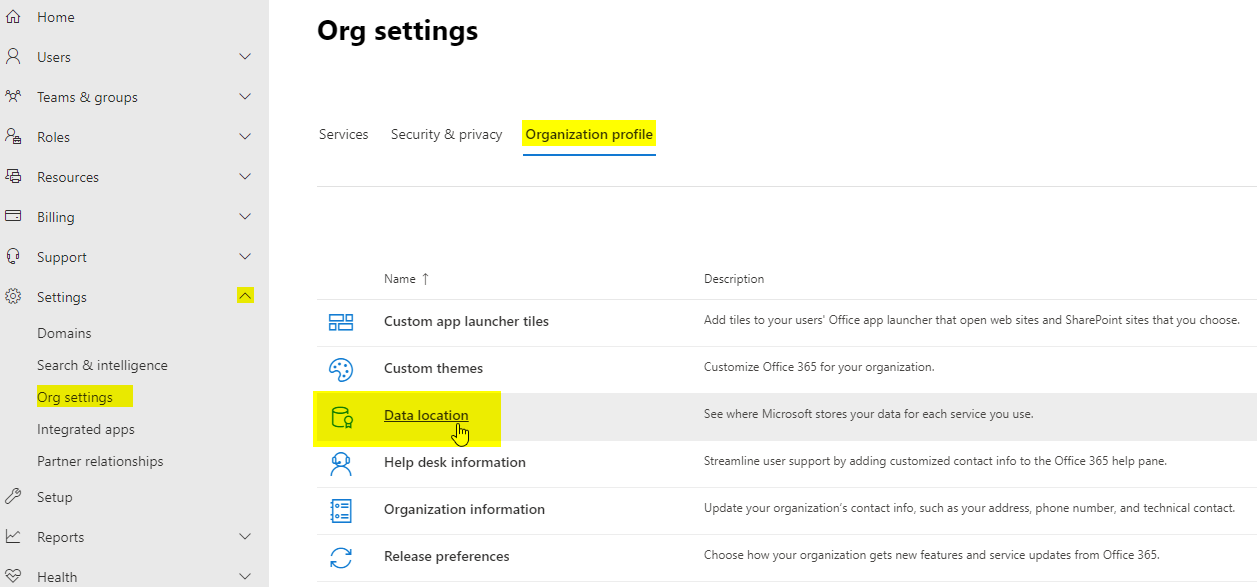
It's always very important to know where your data is (geographically) stored. You can easily check this under Settings, then Org settings, subsequently go to the tab "Organization profile":
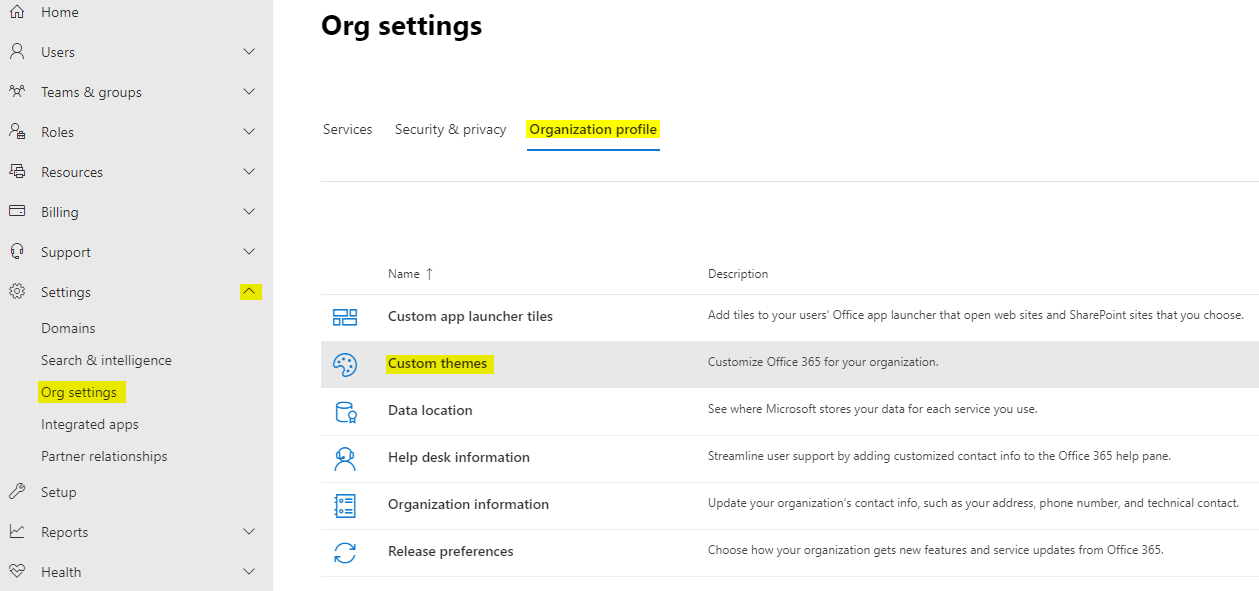
To customize the branding, logos and themes, navigate to the same register as before and choose "Custom themes":
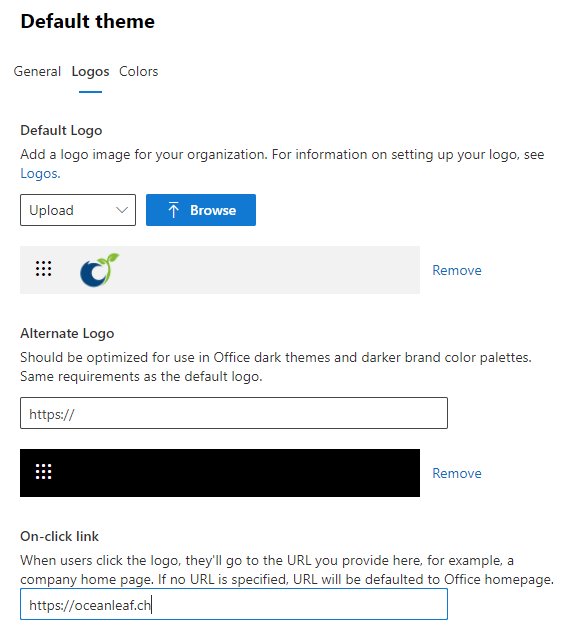
Add a theme at the top and upload the personalized content:
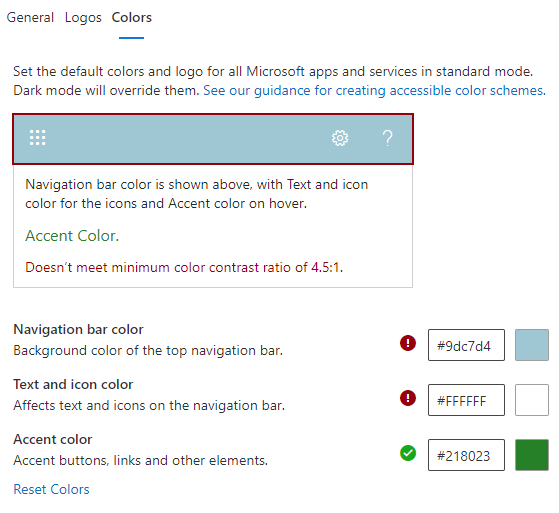
Here you also can set the default colors:
If you miss some settings, be sure that some branding options only get displayed in Azure Active Directory under this link.
Use custom domains
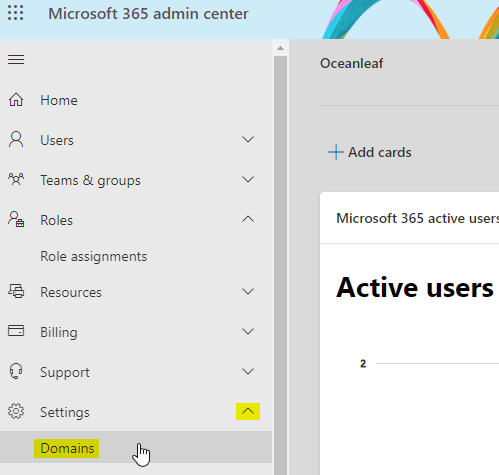
To integrate your own domain names, you first need to aquire one. For example on Namecheap or GoDaddy. Then navigate to the admin center. Go to Settings, then Domains.
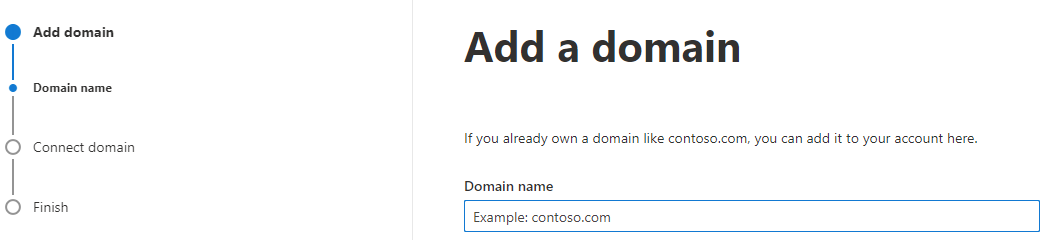
Click on "add Domain" and enter the domain name.
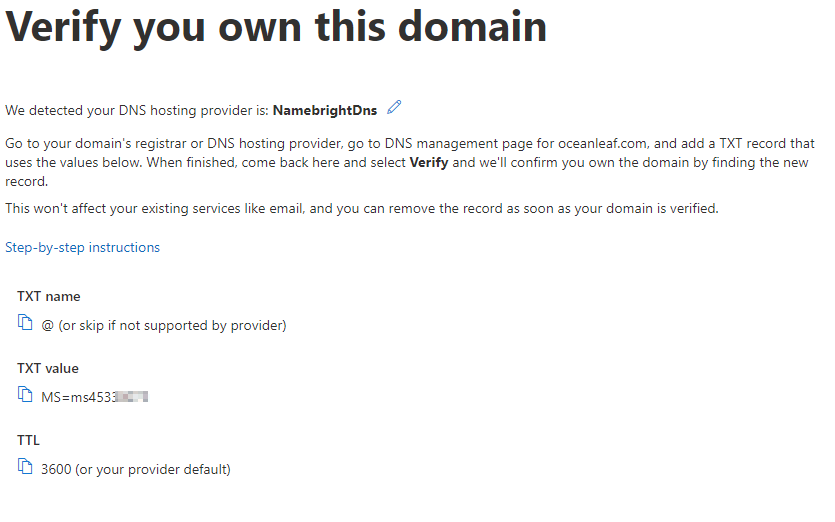
To verify that you hold the domain, it will be also required to add a DNS txt record to the domain.
Connect your domain to Microsoft services
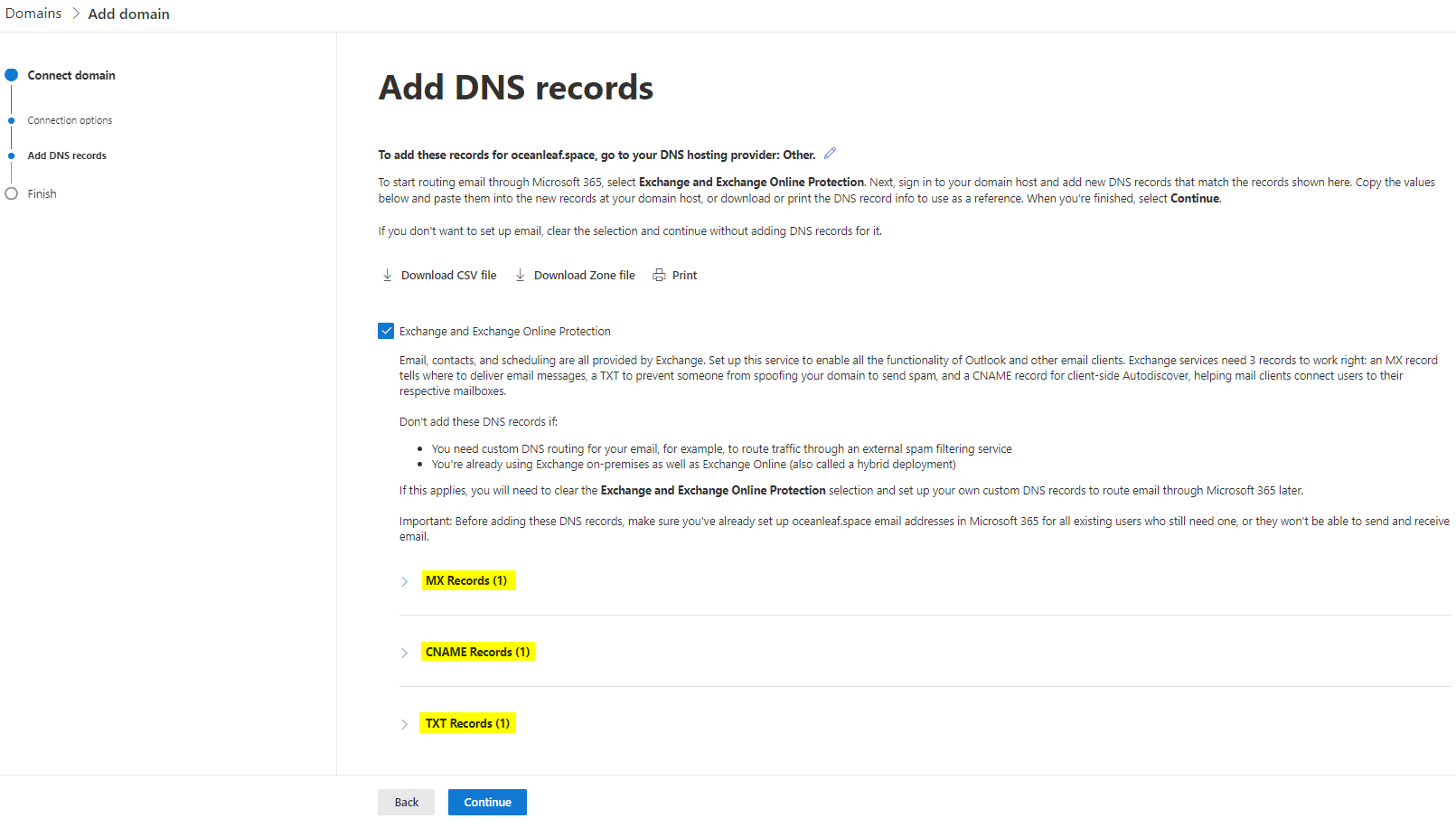
When adding a new domain, a connection to Microsoft services can be established. What you win is email and instant messaging (faster exchange of mails) and Exchange Online protection. To configure, go to Settings, then again Domains.
Productivity & collaboration
How does Microsoft 365 enable your business to achieve more?
There are following productivity & collaboration products available:
SharePoint
Is a central place to store, organize, share or access information. The content's found in it are usually:
- Sites - comparable with team, web or intranet sites
- Document libraries - are online file shares, like in File Explorer
- Apps - other applications can be integrated
In the admin center, it is possible to administer (external) sharing, access control, storage, content types and also OneDrive administrative tasks.
Teams
Is a collaboration platform, that allows to communicate to different teams, organize projects or bring interests together.
The Teams admin center let's you control org-wide settings, teams, messaging policies, integrated apps, analytics & reports and more.
Exchange
Exchange forms the base of e-mail services. The counterpart (client) is Outlook.
Various actions are achievable in the Exchange admin center. Most often used are: Mailbox management, mail flow rules, migrations and insights.
Managing devices
Endpoint management with Windows, iOS, Android or MacOS is possible with Microsoft Intune. This is what I mostly write about on this blog, so feel free to check out my tutorial series on Intune Endpoint Management.
Security
So please be aware that just because you are in the cloud doesn't automatically mean that you are secure. We just encounter different challenges and use other solutions. These are some of the best practice solutions in the field, which I recommend setting up:
If you want to dig deeper in this topic, check out my security related posts from the past: Microsoft 365 security concepts and M365 security landscape.
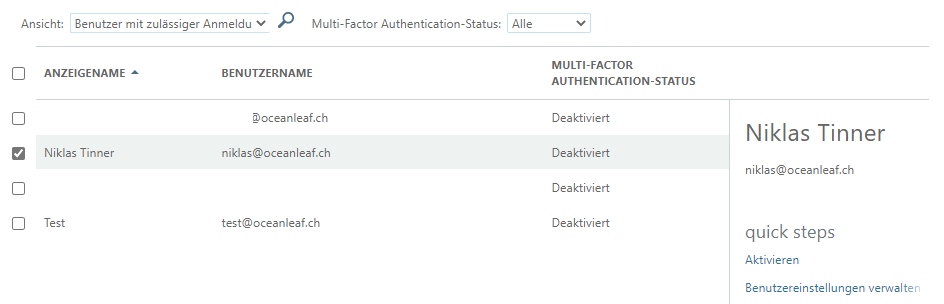
MFA
Multi-factor authentication is a key perimeter in every environment. The setup is easy, but in case of an attack the best protection on identity level. To enable MFA for a specific user go to M365 admin center, Users, Active users and choose Multi-factor authentication at the top. In a new page you can activate MFA for individual users.
Conditional access
Now if you wan't to build a dynamic and advanced resistance with Identity + Access management, Conditional access is the way to go. Read more about Conditional access. If you want to know more, read on some Conditonal access examples. Although this product needs Azure AD Premium P1 license.
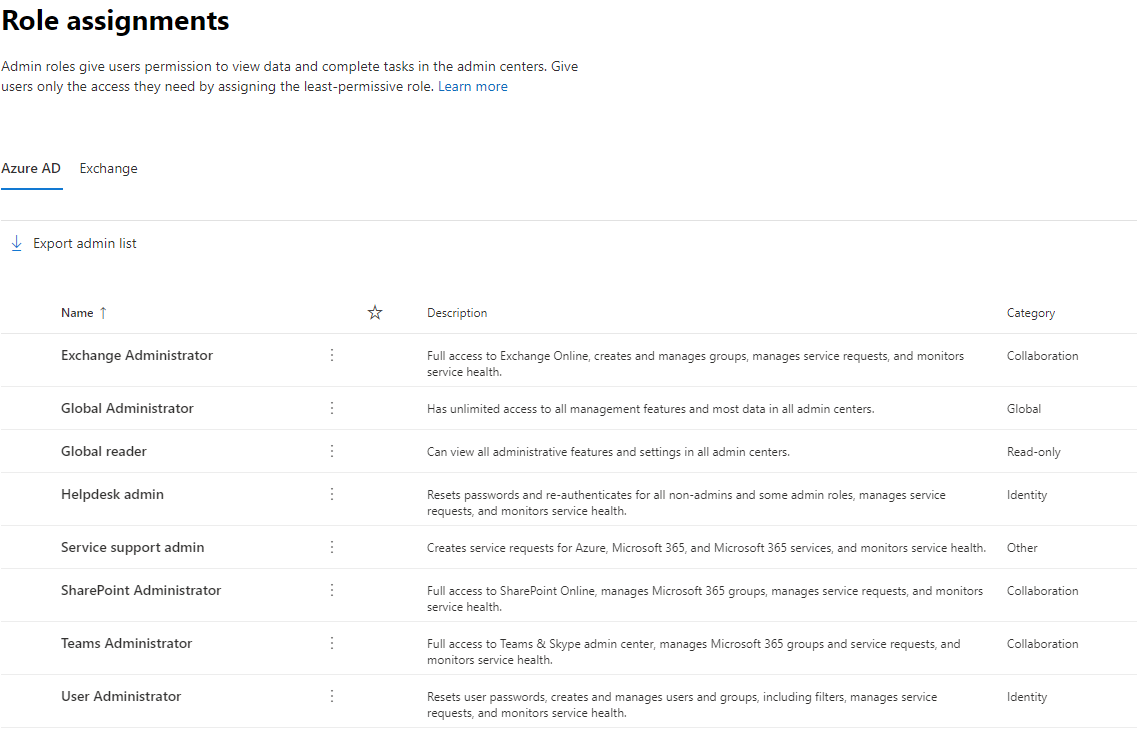
Privileged roles
Treat your privileged roles with a special approach. First of all, be aware of the accounts which have these privileged permissions. Those are found in the M365 admin center, under roles.
Governance to all of them is essential. MFA is strongly suggested and Global Administrator count should be as low as possible.
A breaking glass admin describes a non-personal Global Administrator, whose password only exists on paper and is used only in an emergency. This account is excluded from all policies.
Enterprise applications
Collaboration with other cloud apps offer barely anything. But the control to these interfaces should be controlled or restricted. Enterprise applications & registration help you to manage this job. Open the Azure Active Directory admin center and go to Enterprise applications. Each of the entries here represents an app that your users had an interaction with.
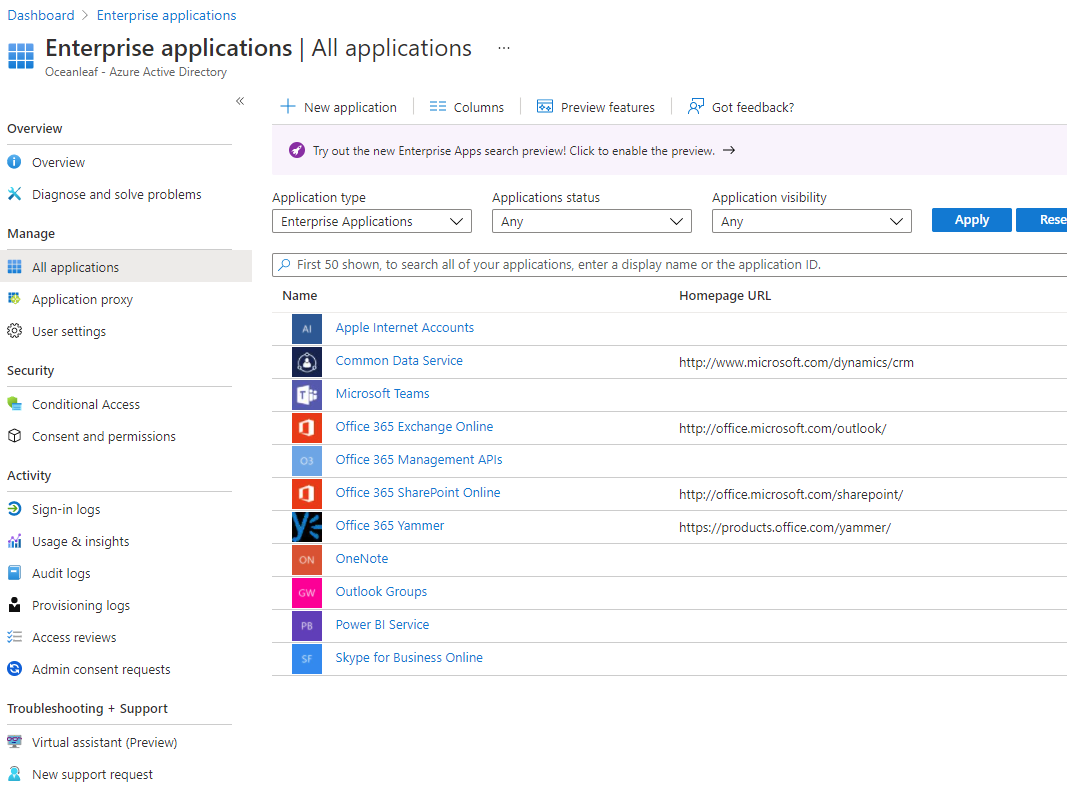
To secure and have data control understand my blog post about identity federation and application management in Azure AD.
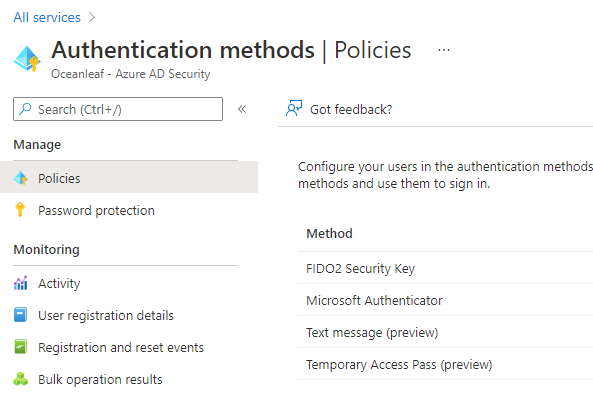
Authentication methods
A username + password in the cloud world can closely be stated as legacy. The alternatives are passwordless with MFA included. You can and should configure these methods in AAD:
SSPR
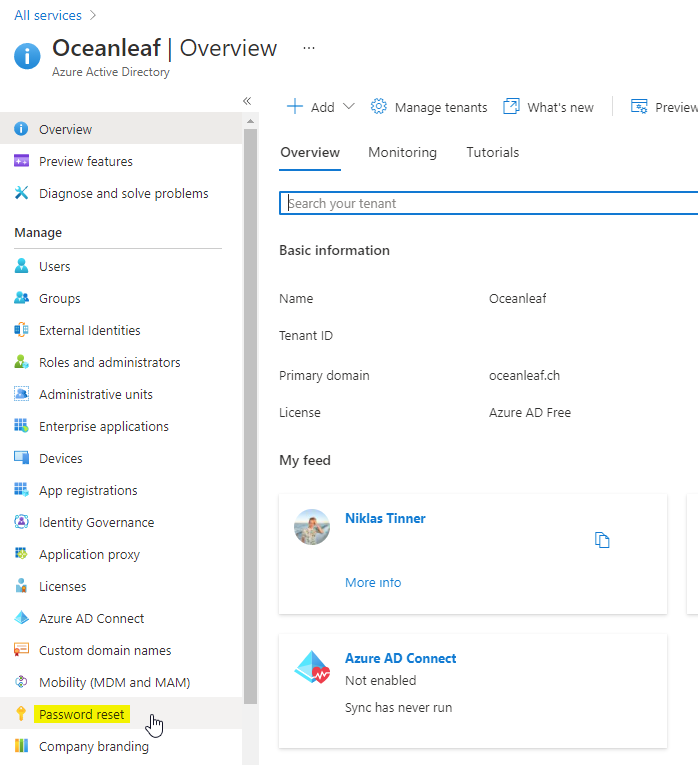
Self-service password reset allows users to reset their own password without the help of an IT administrator. As prerequisite he needs to register his personal security information (MFA) to prove his identity. Activation can be found in AAD:
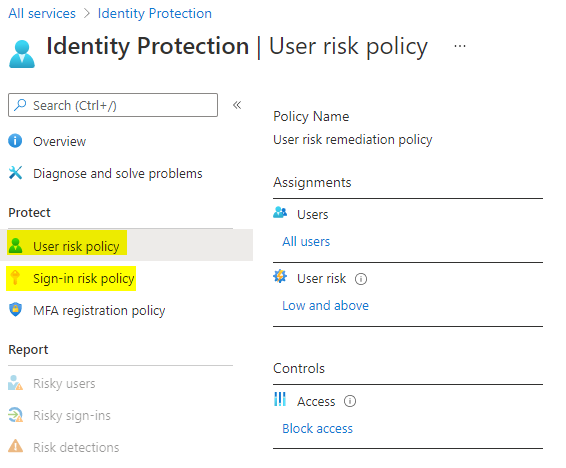
Identity protection
Identity protection secures user & sign-in on different attempts. What you can configure is a general risk level, where specific actions must be taken. For example if Microsoft detects a login from a new device, location or into a new app, the user risk level might be set to medium or even high. If this is rated in a higher level, it my be automatically forced to do MFA, reset your password or you access gets blocked completely. Note: this is an AAD Premium P2 feature.
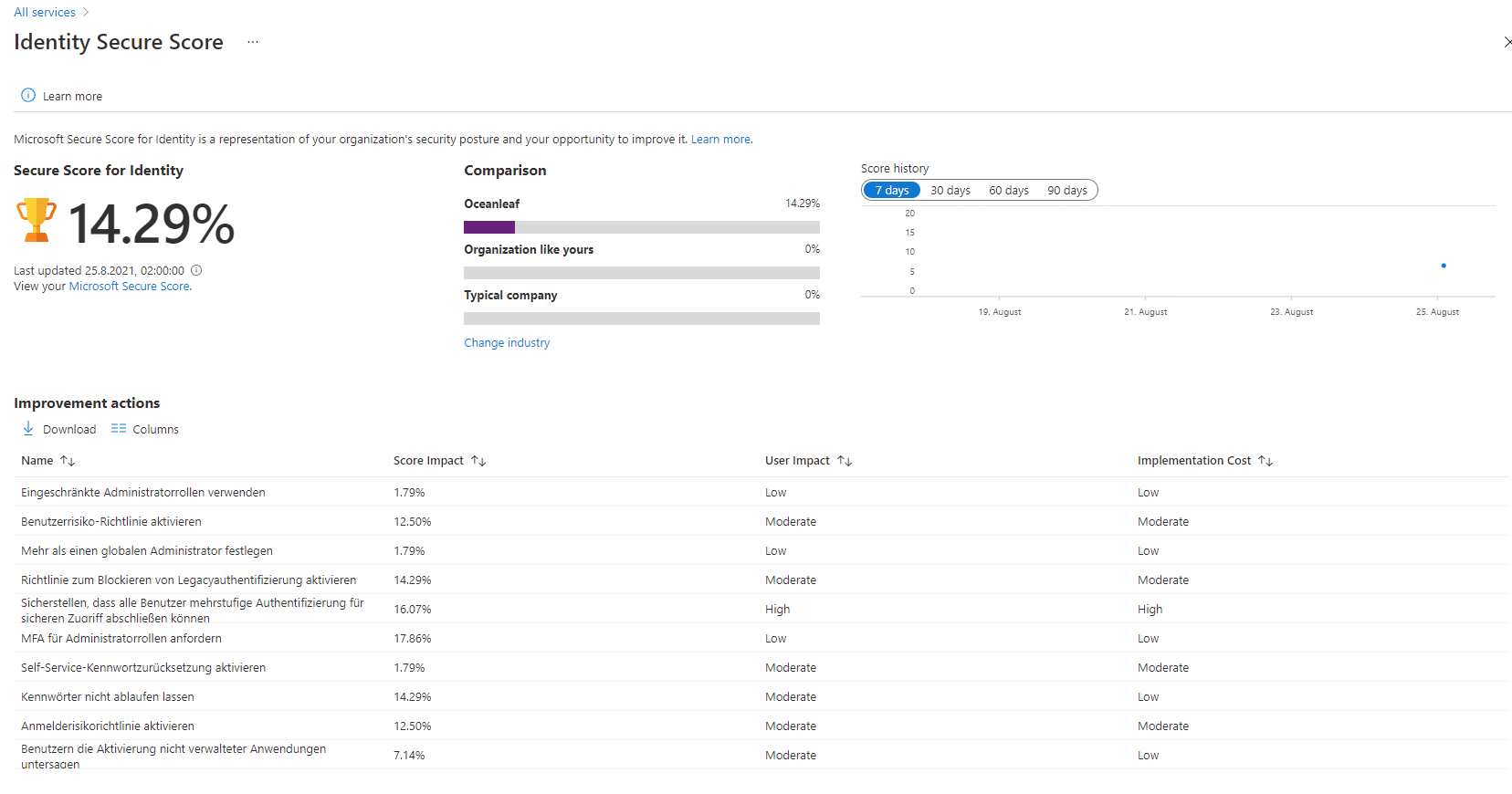
Secure score
Security is such a divers and sophisticated topic that it can be hard to know exactly what to follow along. The secure score is found in multiple Microsoft products and helps increasing the overall security configuration and cloud posture.
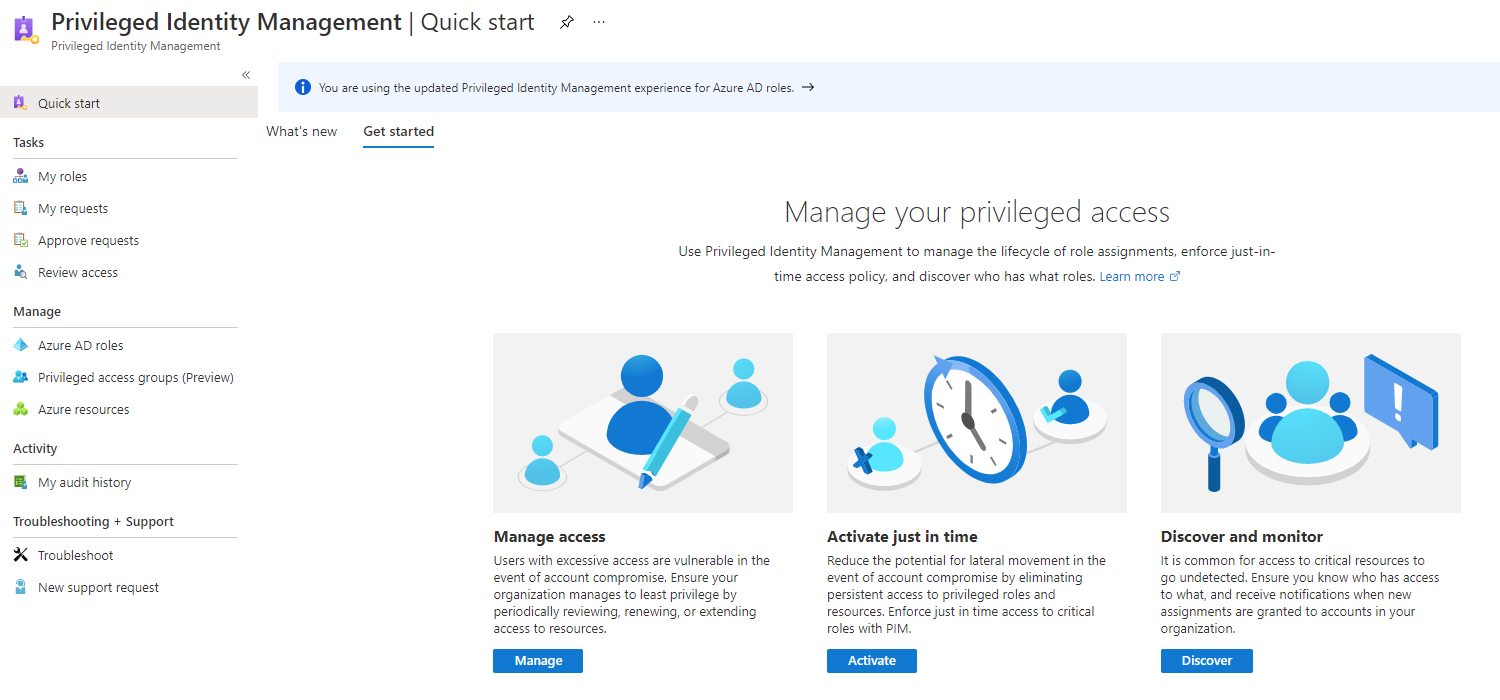
PIM
Privileged Identity management is a solution that helps you to implement JIT & JEA concepts (just in time & just enough access). Users must send request for a role activation or elevation (for example: Exchange Administrator) and a approver group is able to review these requests, allow or deny them. This is also a AAD Premium P2 feature.
Defender for Office 365
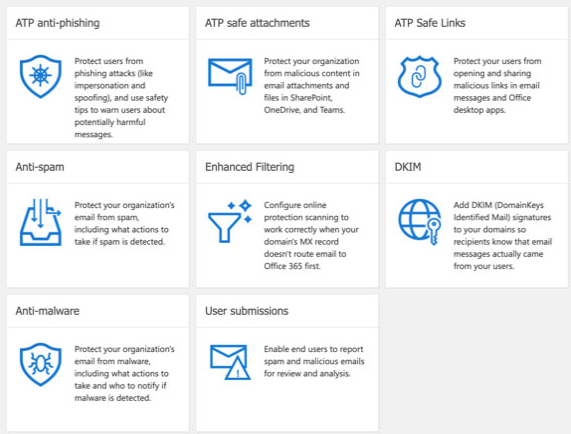
For even comprehensive security in Office products, you should consider Defender for Office 365. Therefore a new license plan is compulsory. But in the end this can constitue the whole Office & web content security, which does play a major role in attacks.
I may refer you to my post on Microsoft 365 security landscape to learn more about how to protect Microsoft 365 online services.